Directory Services Protector

Evaluating Identity Threat Detection & Response (ITDR) Solutions
Active Directory is involved in 9 out of 10 cyberattacks. How can organizations best protect their enterprise identity infrastructures? For this report, we surveyed IT and security leaders at more than 50 enterprise organizations to determine the most valuable capabilities of today’s identity threat detection and response (ITDR) solutions. New…

Protect Your Identity Assets with Purple Knight and Forest Druid
Identity Threat Detection and Response (ITDR) is one of the most talked-about security trends this year. Why? Because your identity systems—Active Directory (AD) and Azure AD for most organizations—are a Tier 0 asset that hold the keys to all your IT and business operations. That makes AD a juicy target…

Evaluating Identity Threat Detection and Response (ITDR) Solutions
What are organizations looking for in Identity Threat Detection and Response (ITDR) solutions? Organizations are looking for ITDR solutions that span the entire attack lifecycle—before, during, and after an attack—and offer protection specifically for AD and Azure AD. Darren Mar-Elia, Semperis VP of Products, summarizes feedback gathered at the 2022…

Closing Tier 0 Active Directory Attack Paths with Forest Druid
Active Directory has countless paths adversaries can take to achieve domain dominance. The problem is clear—excessive permissions. But sifting through every group and user relationship is impossible. Forest Druid flips the script, taking an inside-out approach to attack path management. Forest Druid focuses on attack paths leading into the Tier…

Ransomware, Risk, and Recovery: is your Core Identity System Secure?
Active Directory is the heart of many organizations' information systems: It's used for identity management by 90 percent of businesses. But this 20-year-old technology is increasingly under attack by cyber-criminals who use AD to gain access to your network--and your data. Recent incidents like the Hafnium attack on Microsoft Exchange…

Emergency Communications Org Closes AD Security Gaps with Purple Knight
Real Field Story, Micah Clark, Information Technology Director, Central Utah 911 As a public safety 911 dispatch center, a high-stress job, it's normal to lose and hire people regularly, so Active Directory is constantly changing. There are a lot of things happening, including different computers being added or taken off…
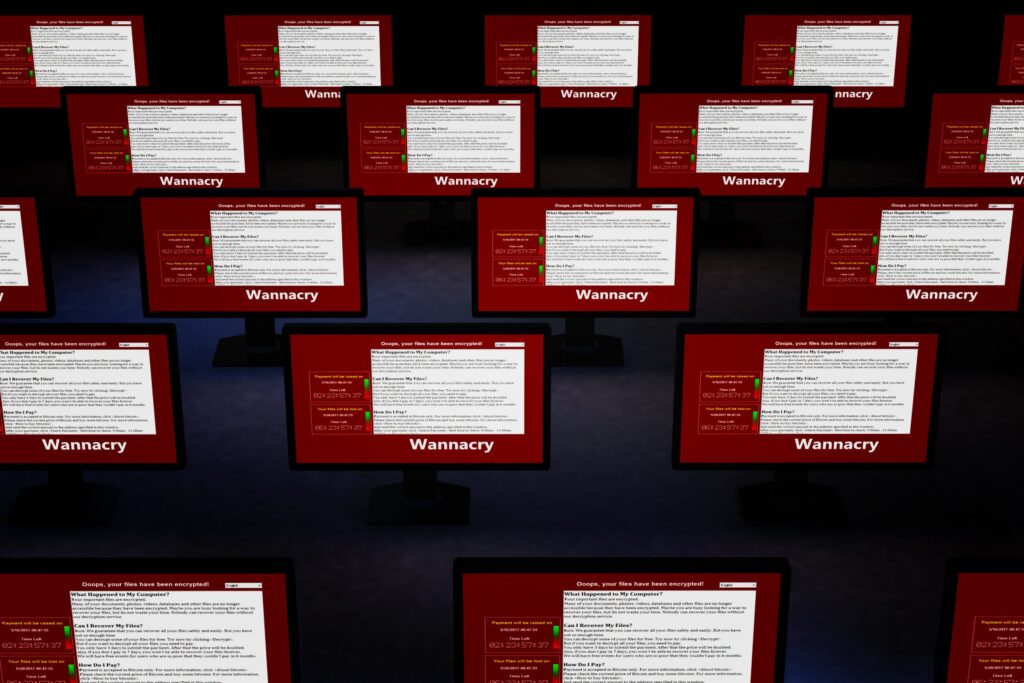
Think Like a Hacker: Defend Your Organization Against Ransomware-as-a-Service Attacks
Government agencies are increasingly adopting software-as-a-service (SaaS) and other as-a-service models to modernize service delivery and increase efficiency. Cybercriminals are too. With ransomware-as-a-service (RaaS) tools, bad actors can use already-developed ransomware methods to execute attacks that are smarter, faster and more sophisticated. As concerns about ransomware attacks have grown tremendously…

Top 10 AD Threats
Most Fortune 1000 companies use Active Directory or Azure AD—and AD is involved in ~90% of cyberattacks. Did you know that there are some relatively simple actions you can take that will significantly increase your chances of fighting off attackers and building your resilience? How can you protect your organization?…

How to Get the Best Cyber Insurance by Demonstrating Operational Resiliency
- Semperis
Live panel discussion with Ed Amoroso (TAG Cyber), Anthony Dagostino (Converge), and Jim Doggett (Semperis) With the rise of ransomware and cybercrime, having an effective cyber insurance policy in place is part of a layered defense strategy. But the cyber insurance industry is in a state of flux as the…

Resurrecting Active Directory After a Ransomware Attack
Jorge has been a Microsoft MVP since 2006 with a specific focus on designing, implementing, and securing Microsoft Identity & Access Management (IAM) technologies. Holding various Microsoft certifications, his experience includes Active Directory (AD) design and implementation, training, presenting, developing security-related scripts and tools, and developing and implementing AD and…



