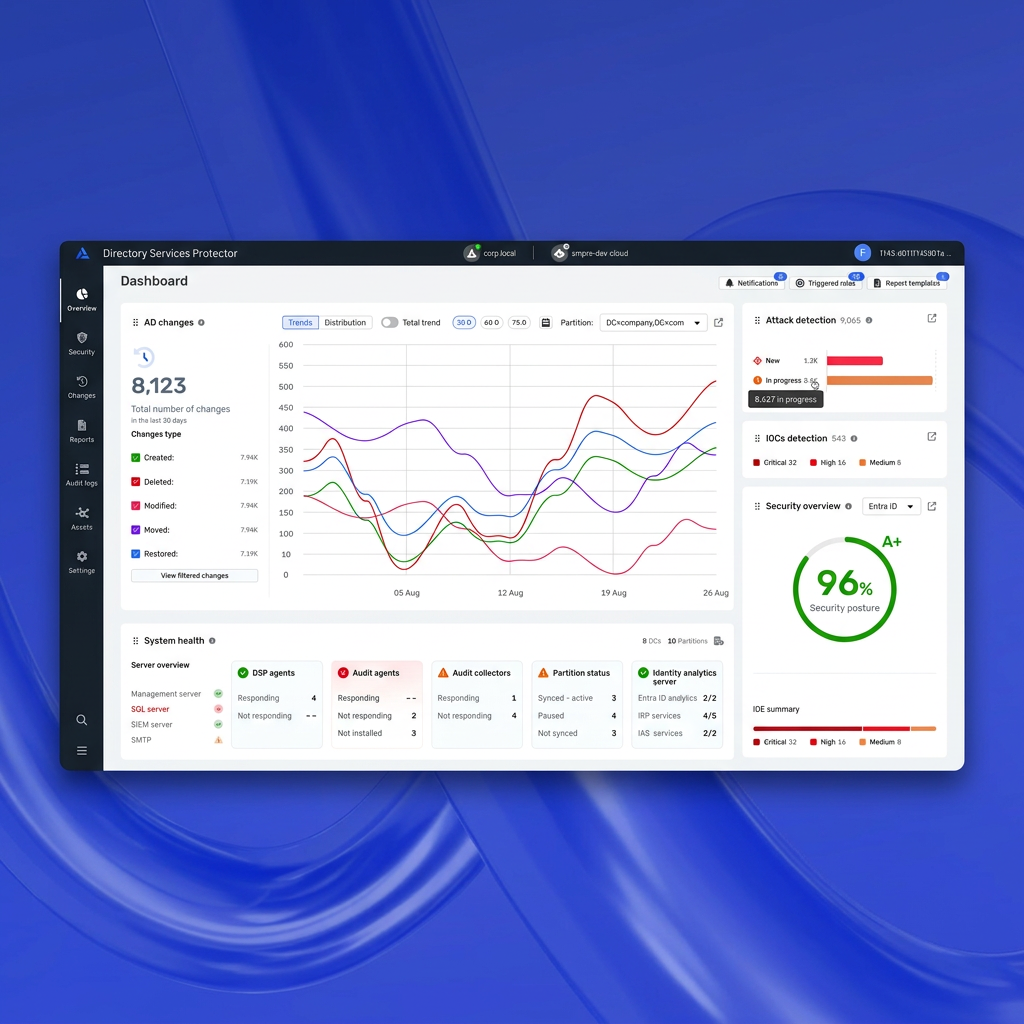
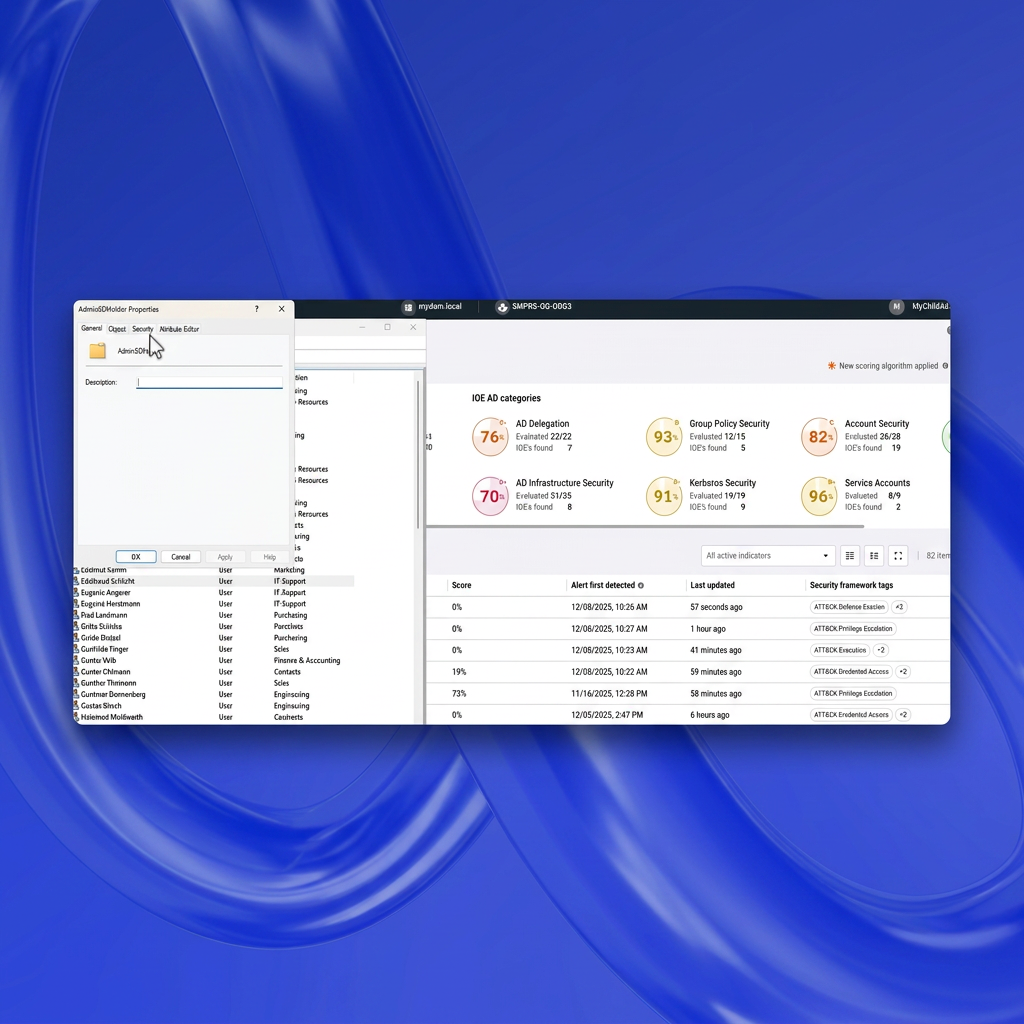
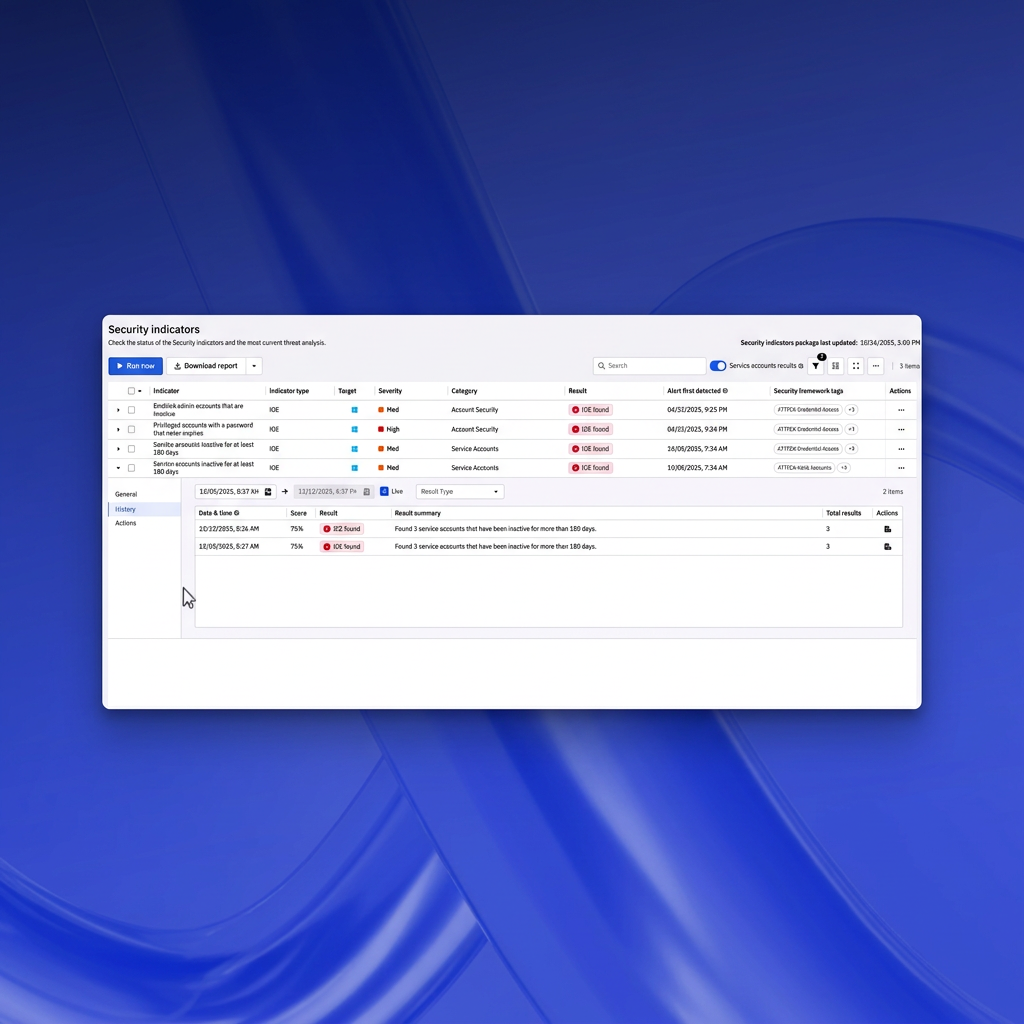
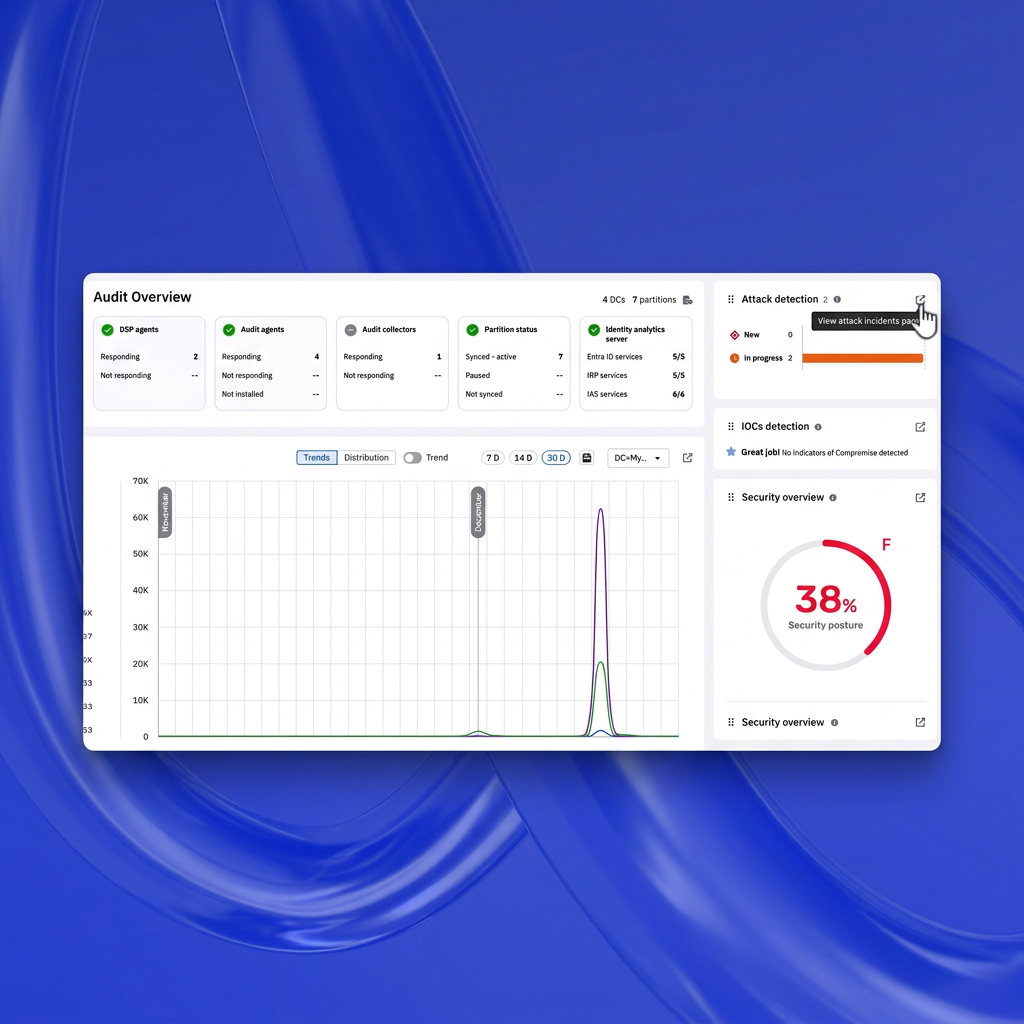
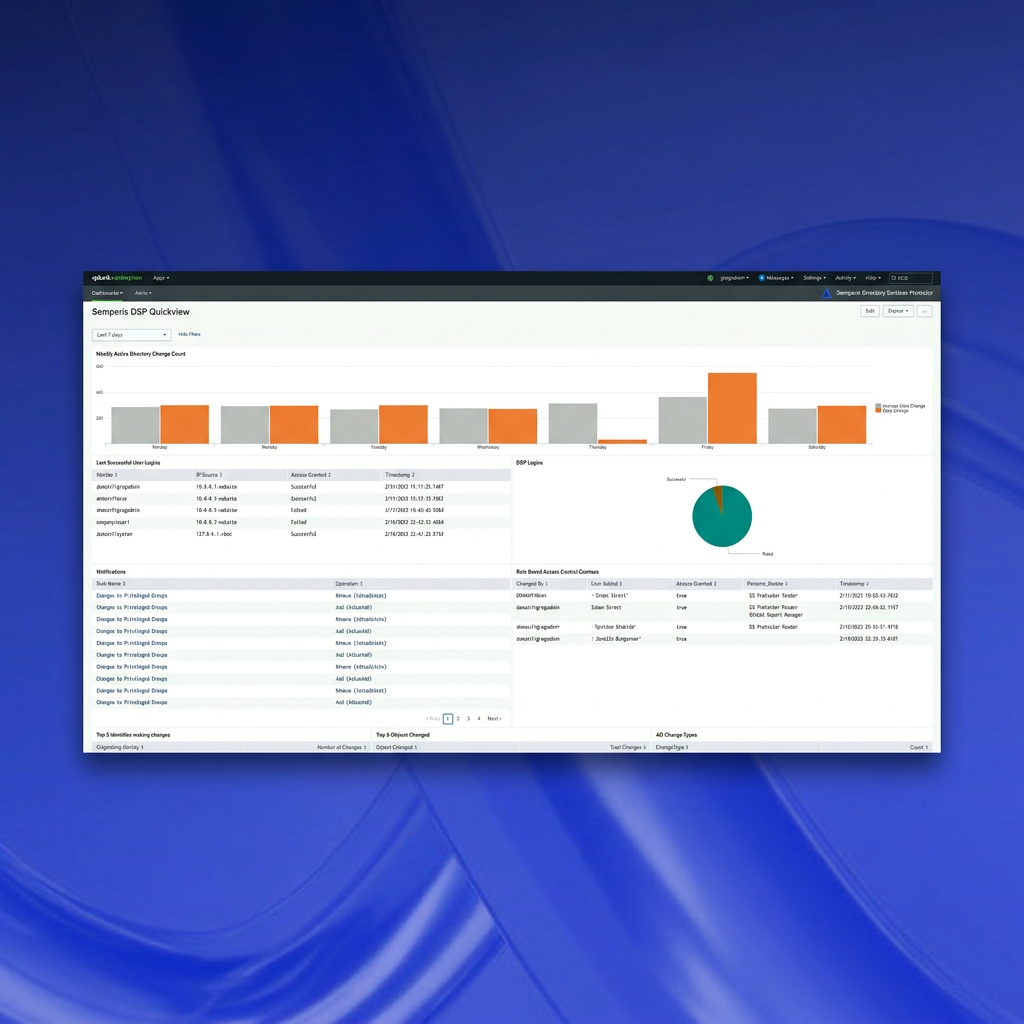
Use hundreds of built-in, constantly updated security indicators in DSP to monitor your hybrid AD/Entra ID environment for legacy vulnerabilities and emerging threats. See status in a clear dashboard that highlights severity levels, so you can quickly prioritize actions to improve security posture.
- See overall security posture score in a clear dashboard
- View security indicator status by severity level at a glance
- Get hundreds of security indicators constantly updated by an in-house expert threat research team
- See AD and Entra ID vulnerabilities in a single dashboard to catch attacks that move from on-prem to cloud, and vice versa