[Updated February 21, 2024; originally published December 14, 2017] Active Directory is the most critical identity system for most enterprises. The problem is that in the two-plus decades since Active Directory was released, the enterprise security landscape has changed drastically. This has left many organizations vulnerable to Active Directory attacks.
Yet few businesses have adapted their Active Directory environment to better protect against potential cyberattack. Delegations are handled haphazardly. Default permissions on objects are typically optimized for discovery, not security. And in sufficiently large environments, determining exactly how to prevent a malicious threat actor from attacking Active Directory can be challenging.
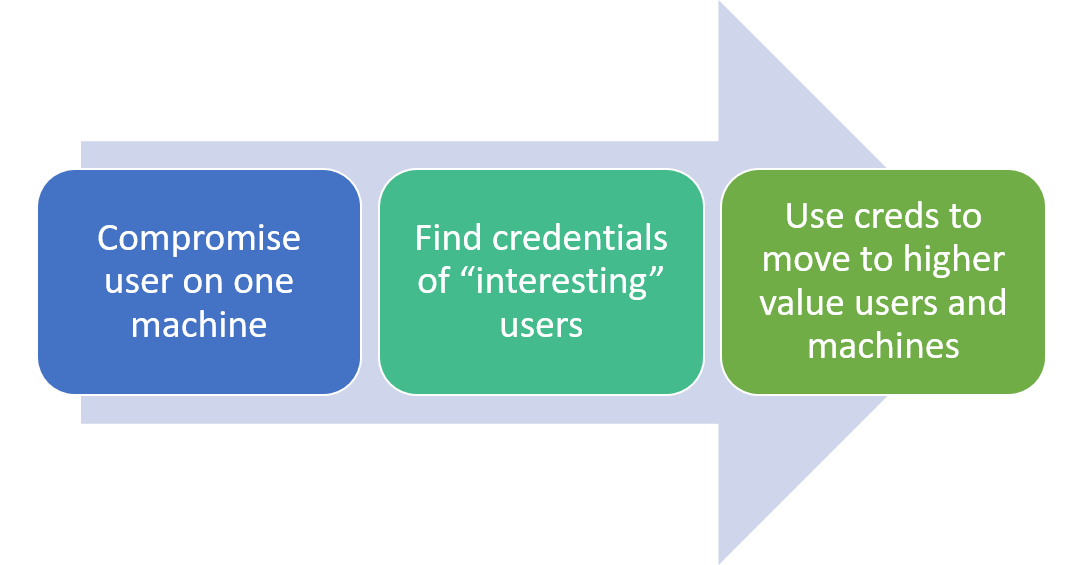
In addition, cyber threats have become more sophisticated. Their aim is no longer compromising single systems. Now, attackers care about finding the quickest paths to your Tier 0 resources—including the identity system. What can you do to protect such a critical asset?
Common points of weakness
Privileged access management in Active Directory has been an obvious problem for quite some time. Building Active Directory with Read access for all Authenticated Users 23 years ago might have been a great idea, but now that’s just asking for a cyberattack.
Many shops have gotten better about implementing rigid policies for Domain Admins. But the next tier of users is even more interesting to an attacker.
This group of users also has access to sensitive information. Most privileged group memberships are readable by Authenticated Users, making their members easily discoverable for attack targeting by a threat actor. If an attacker can gain access to a privileged account and fish around Active Directory, then they can learn useful information about what’s in AD from a privileged access perspective.
With this privileged account access, attackers can then create a blueprint of that Active Directory environment. this is why privileged access management is a crucial part of protecting yourself from Active Directory attacks.
Another vulnerability lies in the fact that non-administrative users might be granted rights to take privileged actions. Think: Who has Reset Passwords rights to your admin accounts? Is it the Domain Administrator or another user group?
Attackers can look at access control lists (ACLs), see who has access to which objects, and use that information to compromise Active Directory. If a helpdesk person can reset passwords on your most privileged users, and an attacker gains access to that helpdesk person’s account, then you’re opening yourself up for domain privilege escalation by the attacker.
5 common Active Directory attack methods
1. Credential compromise
Most attackers gain access to Active Directory through stolen credentials. There are a multitude of methods for compromising an Active Directory password.
Credential theft is a common way to facilitate lateral movement. A Pass the Hash attack, for example, is a Windows-specific instance of credential theft in which an attacker gains access to a server or service by using a user’s password hash rather than the cleartext password. This method involves stealing the LAN Manager (LM) hash or Kerberos keys of a user from LSASS memory on a Windows system.
2. Mimikatz
Mimikatz, described as “a little tool to play with Windows security,” is probably the most versatile and widely used Active Directory exploitation tool. It provides a variety of methods for grabbing LM Hashes, Kerberos tickets, and so on.
3. PowerSploit/PowerView
PowerSploit/PowerView is a PowerShell-based toolkit for recon, exfiltration, persistence, and so on.
4. BloodHound
BloodHound is a graphical tool for finding relationships in Active Directory environments that help speed the path to privileged access.
5. ADFind
ADFind is a simple command-line tool for searching Active Directory and has become very popular as an AD reconnaissance tool.
Measures to protect Active Directory
The good news is that, despite its potential for exploitation, you can do a lot to make it harder for attackers to move around Active Directory.
- Reduce information exposure through privileged AD users and groups, GPOs, and so on. Use resource-based constrained delegation and built-in technologies such as Credential Guard and Remote Credential Guard in Win11 Pro & Enterprise.
- Monitor, monitor, monitor your IT environment using an Active Directory auditing tool. (This great white paper documents lateral movement-related event IDs that can be useful to monitor.)
- Harden privileged groups. For example, the member attribute should not be world-readable; only consumers of that group need access to it. Delegation of Full control or Write of the group’s member attribute should be restricted to other privileged users at the same or higher privilege tier.
- Harden privileged users. Reset password, Take Ownership, or Full control permissions should be tightly controlled to other users at the same privilege tier.
- Harden GPOs that grant privileged access. These GPOs should not be world-readable. GPOs that contain security settings should be restricted on Reads.
- Consider restricting credentials using the Tiered Admin Model presented in Microsoft’s Pass-the-Hash white paper or the more recent Privileged Access Strategy.
Tools to fight threats attacking Active Directory
Taking these preventative measures makes it more difficult for attackers to compromise Active Directory. But once an attacker is hiding in your environment, there’s no way to prevent them from attacking Active Directory and wiping out your environment.
That’s why implementing a disaster recovery solution for Active Directory is the single most critical step you can take to protect your identity infrastructure.
- Semperis Purple Knight and Forest Druid are free community tools that provide security posture assessment and attack path analysis for Active Directory, Entra ID, and Okta.
- Semperis Directory Services Protector gives you visibility over your Active Directory security posture to help you harden Active Directory before an attacker can get in. This tool also monitors any changes happening in your AD so that you can more quickly spot suspicious activity.
- Semperis’ fully automated Active Directory Forest Recovery solution makes recovering from an AD attack as simple as three mouse clicks, reducing your time to restore from weeks to hours.
With all the new techniques that exist for attacking Active Directory, AD security is paramount. Modernizing your identity infrastructure can also help. Still, adopt an “assumed breach” mindset, prepare your AD disaster recovery plan, and keep a reliable incident response resource on speed dial.
