Directory Services Protector

Healthcare Security Fireside Chat: NIST, Identity, and Ransomware
No one can ignore the sharp uptick of hospitals victimized by ransomware. And in healthcare, the stakes are higher. Just last month, a 78-year-old patient at University Hospital Düsseldorf died after a ransomware attack crippled the hospital's IT systems and forced doctors to attempt to transfer her to another facility.…

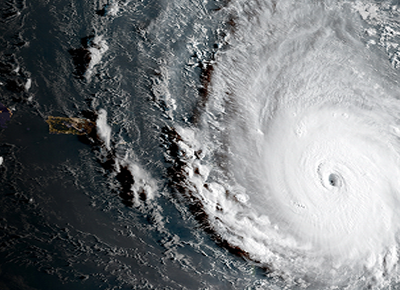
A Cyber-First Approach to Disaster Recovery
In this era of digital transformation, cyber weaponization is commonplace, and the "extinction event" is a genuine threat, especially for organizations with uptime and availability requirements. As we've seen in the headlines, cyber disasters cripple business operations and impact shareholder value. For instance, Equifax just became the first company to…

Seizing the Castle: A Medieval Battle Technique Workshop
The cybersecurity industry is not at a loss when it comes to cheesy castle analogies or quoting Sun Tzu whenever it gets the chance (keys to the kingdom, crown jewels, the art of war), you name it we’ve butchered it. But what if we took some time to look at the whole medieval…
The Dos and Don’ts of Recovering Active Directory from a Scorched Earth Disaster
In the age of cloud, dependency on Active Directory (AD) is rapidly growing — and so is the attack surface. The threat to AD from ransomware and wiper attacks is generally understood, but the complexity of forest recovery is not. In “the good old days,” AD recovery meant recovering AD…
Attacking & Defending Active Directory Workshop
How do you defend Active Directory, aka the “keys to the kingdom,” if you don’t know where the attacks are coming from? Hackers constantly find new ways to break into AD. And once inside, they’re increasingly adept at covering their tracks to silently create backdoors and establish persistent privileged access.…

How to Defend against DCShadow
The DCShadow attack exploits a switch in the Mimikatz utility that enables privileged users to inject malicious changes into Active Directory (AD) without detection. DCShadow takes advantage of native AD replication to avoid sending events to the AD security logs. DCShadow methodology: DCShadow empowers attackers (with admin rights) to spin…
Directory Services Protector for Active Directory
Active Directory is the core IT identity infrastructure system for almost all large global organizations, including those that deploy both Windows and Unix servers. Even organizations using identity-as-a-service (IDaaS) solutions still depend on the ability to populate cloud-based directory accounts and/or to authenticate users from a premise-based AD installation. Should…



