Forest Druid

Business Continuity and Identity System Recovery
- Semperis
Is your disaster recovery plan designed with business continuity in mind? Unless it includes specific procedures for securely recovering Active Directory (AD) and Entra ID, you might be in for a nasty shock. Secure identity system recovery is a key factor in determining how quickly your organization can get back…

Recovering Operations After a Cyberattack
- Semperis
Critical infrastructure organizations that manage operational technology (OT) systems or Internet of Things (IoT) devices face several challenges to effective cybersecurity, including outdated technology, the complexity of diverse environments, and an increased attack surface. Rob Ingenthron (Senior Solutions Architect, Semperis) discusses the challenges faced by organizations in healthcare, manufacturing, energy…

Building a Layered Identity Defense
- Semperis
Cyberattackers are adept at finding ways through your defenses and into identity systems like Active Directory. From there, they can move laterally, escalate privileges, access sensitive resources, and inject malware or ransomware. Implementing a layered defense that includes identity threat detection and response (ITDR) is key to protecting your operational…

Cyber Resilience 101: Top Tips for Active Directory Defense
- Semperis
A secure identity system is the foundation of your Zero Trust architecture. That’s why attackers regularly target Microsoft Active Directory (AD) and Entra ID. Gaining control of these identity systems can give threat actors near-total control of all your systems, access to sensitive data, and the means to devastate your…

Protecting AD: The Foundation of Your Zero Trust Identity Strategy
Cyberattacks are the most critical threat facing modern information technology. Most attacks start with identity compromise. For the past quarter century, identity in the enterprise has been synonymous with Microsoft Active Directory (AD). Therefore, AD is almost always involved in a cyberattack—either as the target or as a route to…

To Hell and Back: Recovering Active Directory During an Attack
- Semperis
What do you do when your endpoint or other initial protections are breached? When intruders are already in your network and have even compromised your Active Directory (AD) forest? This is the true story of a ransomware attack—and how it was stopped. Join Semperis’ Principal Technologist and MVP alumnus Guido…
Identity System Defense for the Healthcare Industry
- Semperis
Cyberattackers have healthcare systems in their sights. By breaching identity systems such as Active Directory and Entra ID, attackers can quickly compromise vital operational infrastructure and sensitive data throughout a healthcare organization. Securing the identity infrastructure is a key step in thwarting threat actors. Join Marty Momdjian, Semperis’ EVP of…
Snackable Active Directory Security: 30 Minutes a Day Keeps the Bad Guys Away
- Semperis
“I just don’t have the time to deal with Active Directory.” How many times have you heard (or said) that? Cleaning up years of AD configuration drift and tech debt can be a daunting task … but not as unpleasant as trying to recover the identity system after a full-blown…
Meine hybride Identität wurde gehackt — was nun?
- Semperis
Die Maxime "die IT von morgen ist hybrid" ist gängiger Standard in der IT-Beratung und bei Cloud-Anbietern. Auch Microsofts neue Sicherheits-Referenzarchitektur ist hybrid, betrachtet die Cloud als "Source of Security". Doch die Schattenseiten zeigen sich deutlich, wenn die hybride Identität kompromittiert wird. Dies bringt Herausforderungen wie Störungen beim Single Sign-On,…

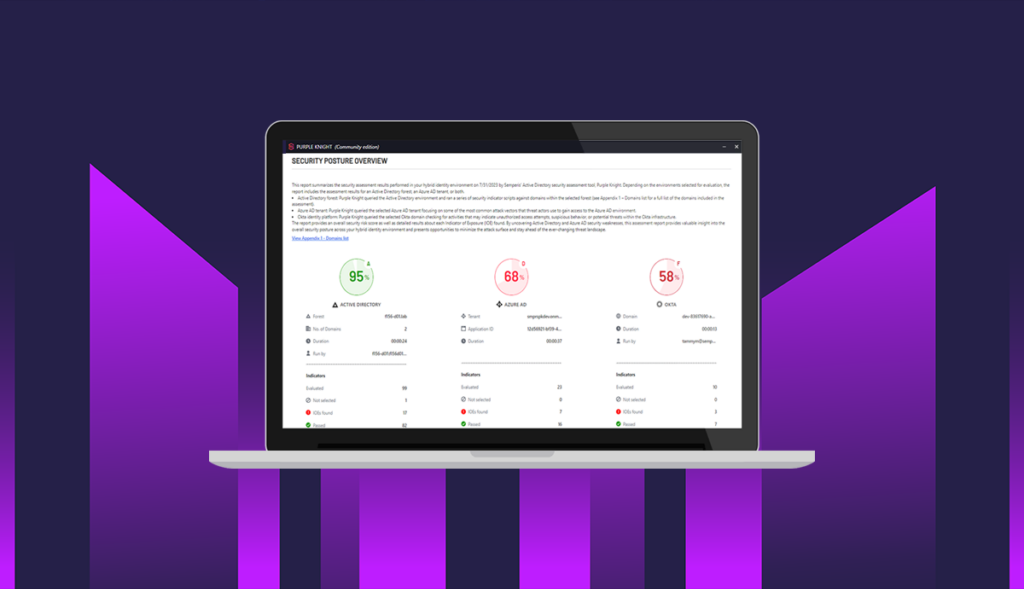
Technology Spotlight on Semperis – ISC2 Canada Virtual Conference
- Semperis Team
Semperis presented at a virtual Canadian ISC2 Chapters Conference, themed "Securing the Future: Embracing Innovation in Cyber Security." Get an overview of the company's Directory Services Protector, Active Directory Forest Recovery, and Purple Knight. Featured presenter: Paul Greeley, Senior Solutions Architect, SemperisPaul has been working in IT for 23 years…



