Forest Druid

Marty Momdjian discusses Ready1 with ISMG Studio at RSAC 2025
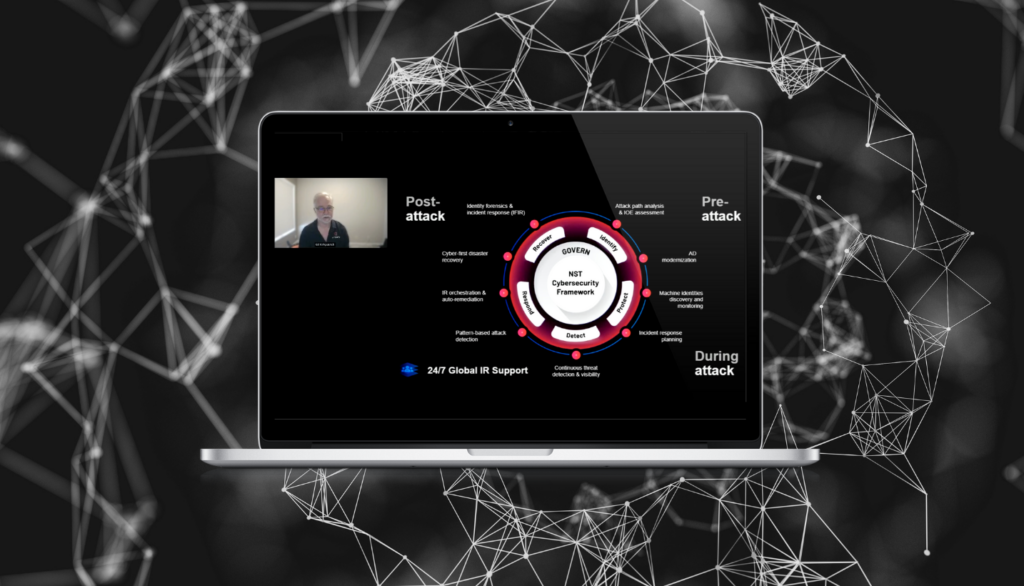
Marty Momdian, EVP Services & Ready1 GM at Semperis, highlights the critical role of incident response in cybersecurity, emphasizing the importance of resilience against cyber threats.

Alex Weinert sits down with ISMG’s Anne Delaney at RSAC 2025
- Semperis
- Jul 24, 2025
For Alex Weinert, being a force for good means empowering cyber resilience—the capability to not only respond to cyber incidents but truly recover. In this interview with Anna Delaney of ISMG, he explains the importance of focusing on identity security and what it means to cultivate a resilience mindset.
AD Security and Recovery: Questions That Need Answers
- Semperis
- Jun 13, 2025
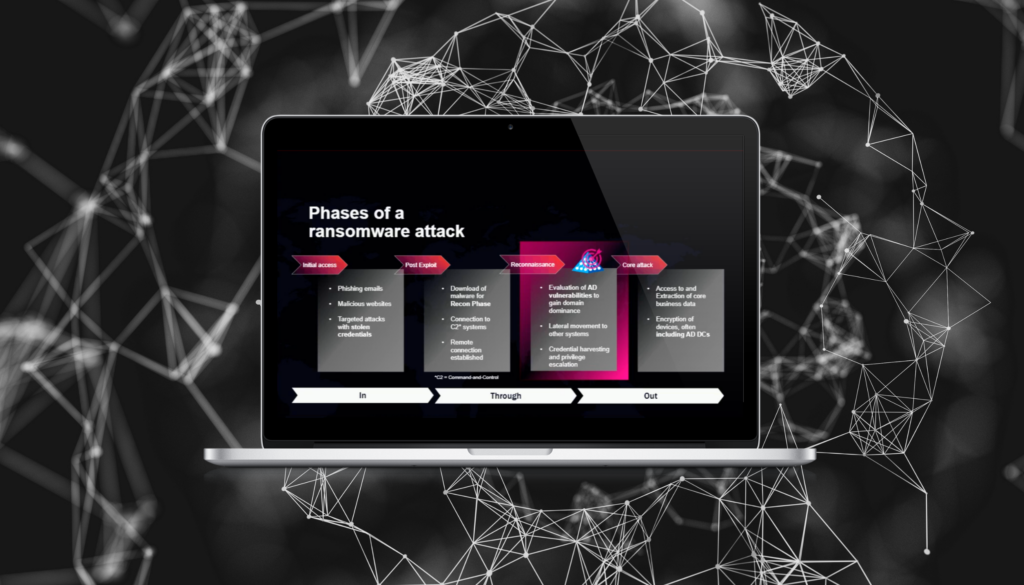
In today’s threat landscape, attackers prioritize identity and access management systems like Microsoft’s Active Directory (AD) because they hold the keys to the kingdom in most enterprises. In other words: Compromise AD, and you control the organization. That’s why modern cyber resilience strategies must focus on AD security, monitoring, and…
NIS2 and Your Identity Infrastructure
Compliance with the EU’s NIS2 directive requires a focus on securing identity systems, which have become a key battleground for cyber defenders and attackers.
ECC-2 and Your Identity Infrastructure
Saudi Arabia’s ECC-2 controls provide comprehensive, standards-driven cybersecurity practices for public and private organizations. Much of their guidance applies particularly to identity systems—the source of access and authentication across most critical business systems.
Five Eyes Alliance Identity Security Requirements: What Federal Agencies Need to Know
Cybersecurity agencies from the Five Eyes alliance, including the Cybersecurity Infrastructure and Security Agencies (CISA) and the National Security Agency (NSA), have urged organizations to strengthen security controls for Active Directory (AD), a prime target for cyber attackers. In “Detecting and Mitigating Active Directory Compromises,” the agencies highlighted more than…
Closing the Gap for Government Agencies: 5 Ways to Automate Cyber Resilience
- Semperis
- May 19, 2025
Operational continuity depends on cyber resilience. Maintaining that resilience can be tricky when resources are scarce. Attackers know this and are skilled at turning staffing turnover and technology gaps to their advantage. Attackers’ favorite means of spreading malware, escalating privilege, and establishing perseverance is the identity infrastructure—typically Microsoft Active Directory…
DORA and Your Identity Infrastructure
Understanding the implications of the Digital Operational Resilience Act (DORA) is crucial, both to meet regulatory demands and to safeguard your identity infrastructure. This white paper provides comprehensive insights into DORA's requirements and practical strategies to enhance your compliance—and your organization's resilience. What's inside: Emerging threat landscape: Explore the latest…

Why Is Your AD an Easy Target for Hackers?
- Semperis
Active Directory (AD) remains a cornerstone for many organizations, both on premises and integrated with Microsoft Entra ID in the cloud. Alarmingly, 90% of cyberattacks target AD, the central identity system for most enterprises. Semperis provides comprehensive protection for on-premises AD and Entra ID, offering continuous defense against identity-based threats before,…
How to Recover Active Directory When Every Second Counts
- Semperis
Microsoft Active Directory (AD) is a key target for cyberattackers. When AD goes down, so do your operations. Yet most organizations lack an AD-specific recovery plan or rely on manual recovery, which can take days if not weeks. Auditing your AD security stance and maintaining a solid incident response plan…



