Forest Druid
Protect & Recover AD and Entra ID — The Keys to the Kingdom
- Semperis
In this on-demand webinar, Rob Ingenthron, Senior Solution Architect at Semperis, will delve into the significance of AD protection and recovery in identity threat detection and response (ITDR). Attendees can expect to: Discover effective strategies for integrating AD protection and recovery into a comprehensive ITDR approach. Gain a deeper understanding…

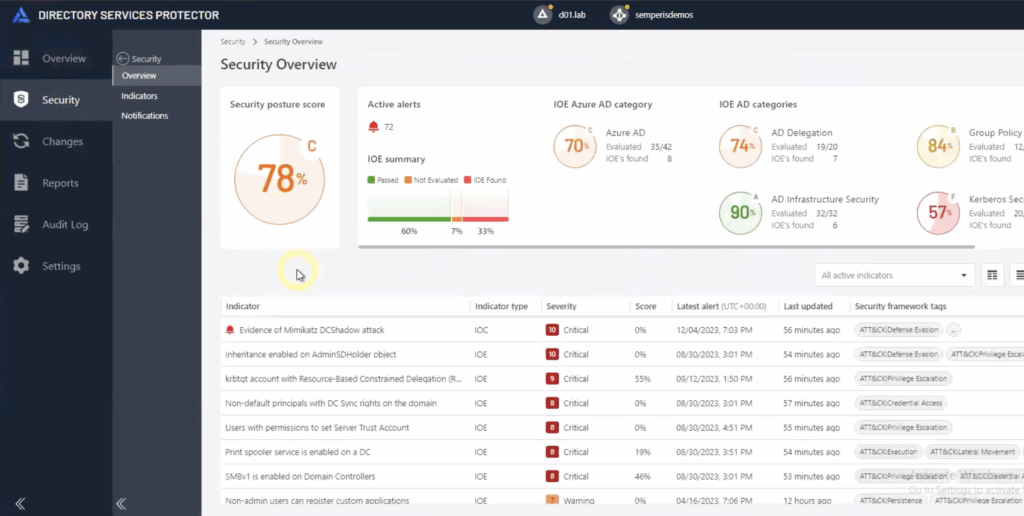
Would your Organization Fail an Identity Assessment?
In this interactive webinar, Kriss will take participants on a journey to explore whether or not their organizations would pass or fail an identity assessment. Drawing from his years of hands-on experience and using Semperis community tools, Kriss will provide valuable insights into common pitfalls, best practices, and real-world examples…
How Semperis Maps to MITRE ATT&CK, Essential8 (AU) & CCoP (SG) Frameworks
Security frameworks have been developed by government and security organisations to help companies and governments alike develop a baseline of minimum cybersecurity practices. In this webinar we will explore the Mitre Att&ck framework, as well as Essential8 from Australia and CCoP from Singapore to understand how Semperis technologies map to…

Closing Tier 0 Active Directory Attack Paths with Forest Druid
Active Directory has countless paths adversaries can take to achieve domain dominance. The problem is clear—excessive permissions. But sifting through every group and user relationship is impossible. Forest Druid flips the script, taking an inside-out approach to attack path management. Forest Druid focuses on attack paths leading into the Tier…

Resurrecting Active Directory After a Ransomware Attack
Jorge has been a Microsoft MVP since 2006 with a specific focus on designing, implementing, and securing Microsoft Identity & Access Management (IAM) technologies. Holding various Microsoft certifications, his experience includes Active Directory (AD) design and implementation, training, presenting, developing security-related scripts and tools, and developing and implementing AD and…

Reverse Engineering a Hackers Approach to Breaking into Healthcare
What do hackers want from healthcare? And how can healthcare CIOs protect vital identity infrastructure from attacks? Guido Grillenmeier, Chief Technologist at Semperis, and Matt Sickles, Solutions Architect at Sirius Healthcare, walk This Week Health through the use of Purple Knight, a free tool for your Identity Threat Detection and…

So You’ve Been Breached – What Now?
Attacks are inevitable and breaches are probable, particularly where your Active Directory is concerned. What is the correct path to take if you have been attacked? Join breach prevention and incident response experts from Semperis as they provide best practices to ensure you recover quickly, completely, and in a more…
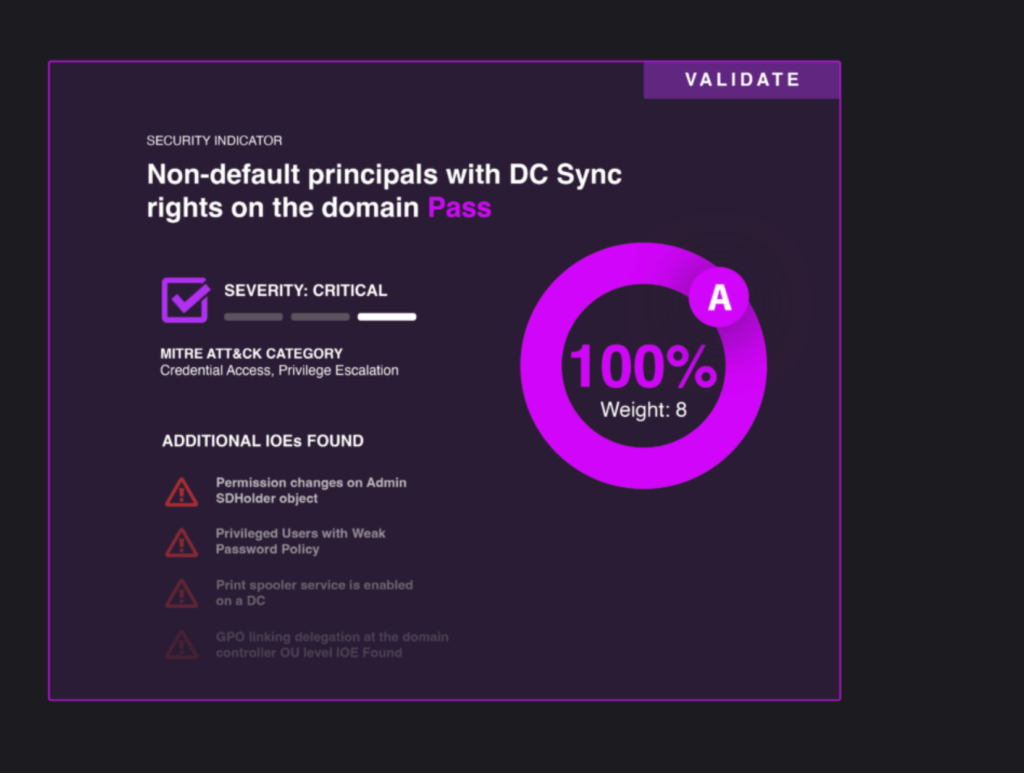
Would Your Organization Fail the Active Directory Security Assessment?
As cyberattacks proliferate, many organizations are investing resources in plugging holes in their security strategy. But one common attack entry point—also used in the SolarWinds breach—is consistently overlooked: Active Directory. According to results from a new security assessment tool that evaluates security weaknesses in Active Directory configurations, even large organizations…
The Dos and Don’ts of Recovering Active Directory from a Scorched Earth Disaster
In the age of cloud, dependency on Active Directory (AD) is rapidly growing — and so is the attack surface. The threat to AD from ransomware and wiper attacks is generally understood, but the complexity of forest recovery is not. In “the good old days,” AD recovery meant recovering AD…



