- The modern identity landscape
- What is the Minimum Viable Company and how does it apply to identity?
- A day in the life of Megakorp
- The Board’s perspective: Downtime is more than an IT problem
- Megakorp and the 5 Ps
- People: The human element of the MVC
- Flexibility and fault tolerance during recovery
- Why Megakorp avoided system state and bare metal recovery
- Beyond the MVC: A staged recovery approach
- Worst. Day. Ever.
- Business resilience: From survival to stability
- Building the wider MVC on a foundation of identity
- After the dust settled
- Additional resources
Modern enterprises cannot operate without identity. When identity systems fail, the business stops. Should your organization experience a cyberattack or other cyber crisis, the ability to quickly recover identity systems to a reliable, secure state is the first step in recovering your Minimum Viable Company (MVC), sometimes referred to as the Minimum Viable Business (MVB). And that is the first step in getting your entire business back online.
What is the MVC, how do you determine it, how does it relate to identity, and how can you ensure its recovery?
To answer these questions, let’s examine a fictional company: Megakorp, a developer and manufacturer of enterprise-grade industrial automation components used by other manufacturers around the world.
Note: This blog focuses on recovery of the on-premises Minimum Viable Company. I’ll cover cloud-based MVC recovery scenarios in my next post.
The modern identity landscape
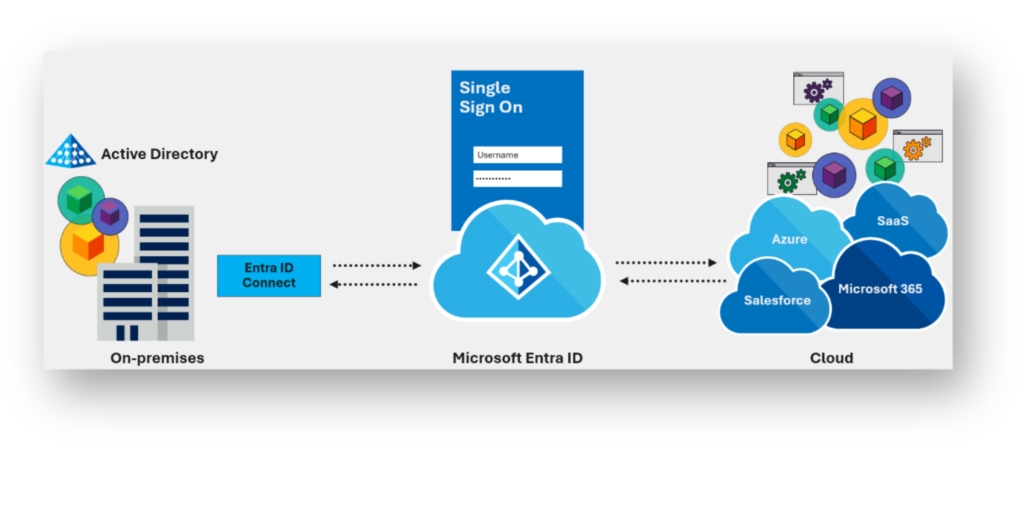
In the modern enterprise, almost everything extends from identity. That’s why we now consider identity as the modern security perimeter. For most organizations, identity begins with Active Directory (AD) and then extends to the cloud (e.g., Entra ID, Okta) to support modern SaaS-based applications (Figure 1).
What is the Minimum Viable Company and how does it apply to identity?
Global professional services firm KPMG defines the Minimum Viable Company as “the smallest possible version of an organization that can still function and serve customers should an incident bring down part(s) of the operations and systems.”
PwC defines the MVC as “identifying the essential services, processes and functions that must remain operational to keep the organization financially, operationally and strategically viable in a crisis.”
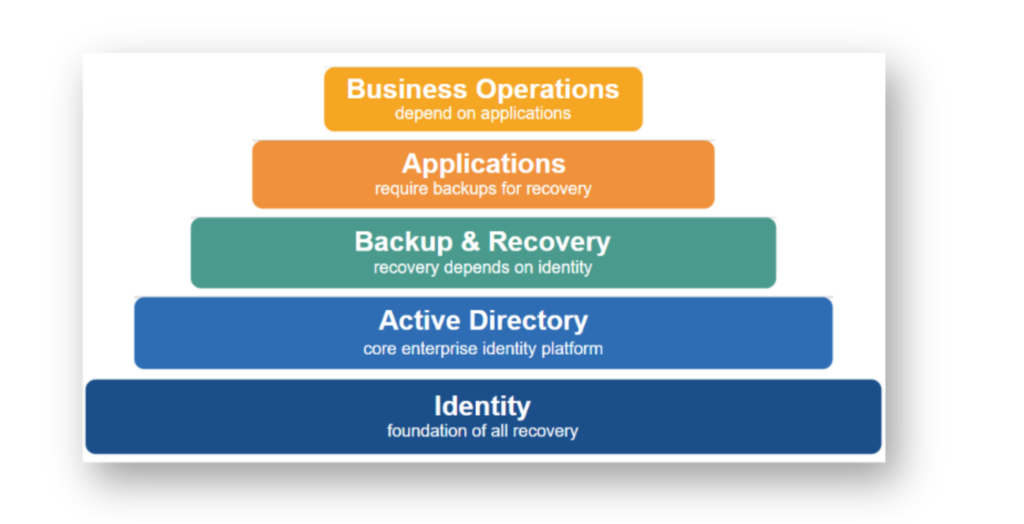
Because identity is foundational to business operations, it is the most important component of your Minimum Viable Company. Without a functioning identity infrastructure, users can’t authenticate, applications can’t start, VPN fails, and admin access is impossible.
A day in the life of Megakorp
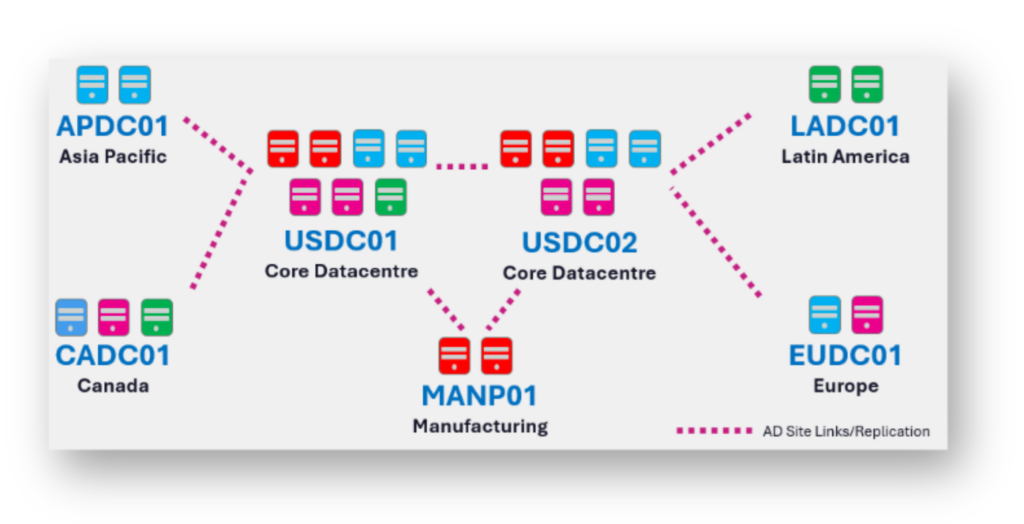
Like many modern enterprises, our fictional example, Megakorp, extends its on-premises identities to Entra ID to support SaaS-based applications such as Microsoft 365. Figure 2 illustrates the Megakorp Active Directory environment under normal operating conditions.
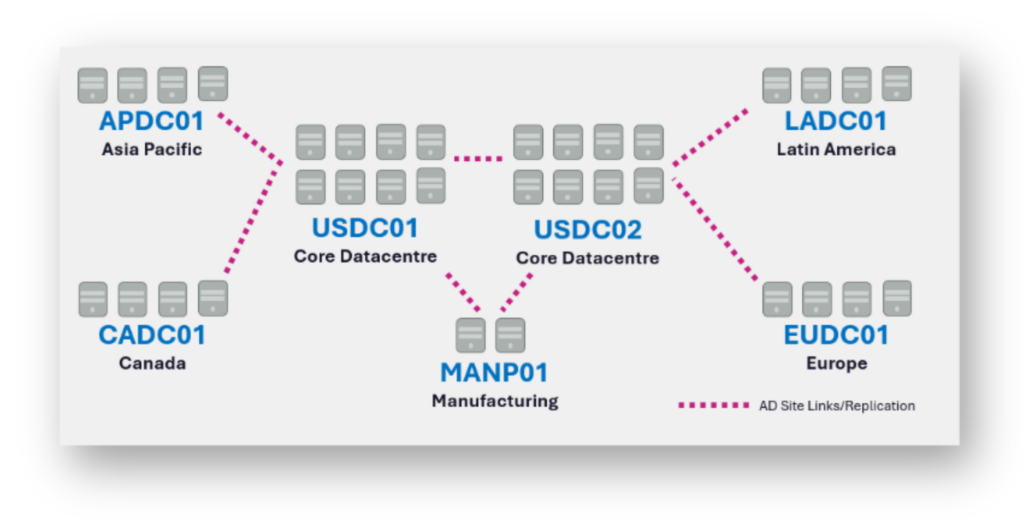
As this diagram illustrates, Megakorp operates two core data centers that host and service critical infrastructure workloads such as VPN, RADIUS, ERP, SQL, Entra ID Connect, and backup and recovery systems. Connected to these core data centers are several regional locations, as well as a highly critical manufacturing plant.
The Board’s perspective: Downtime is more than an IT problem
As a supplier of critical components to manufacturers worldwide, when Megakorp stops, its customers stop, too.
The Megakorp Board understood that a prolonged outage would not just be a financial event, but a reputational one. This reality drove the organization to treat resilience not as an IT metric, but as a business-critical imperative.
Based on previous incidents reported in the news involving similar organizations, Megakorp set out to define and understand what the Minimum Viable Company meant for its business. Recognizing that true cyber resilience does not begin during an incident but months or even years beforehand, the executive Board mandated a program of research, documentation, and analysis.
Megakorp and the 5 Ps
What are the 5 Ps? Proper planning prevents poor performance.
Megakorp introduced playbooks, runbooks, tabletop exercises, and continuous refinement to ensure that the organization could respond swiftly and confidently should the need arise.
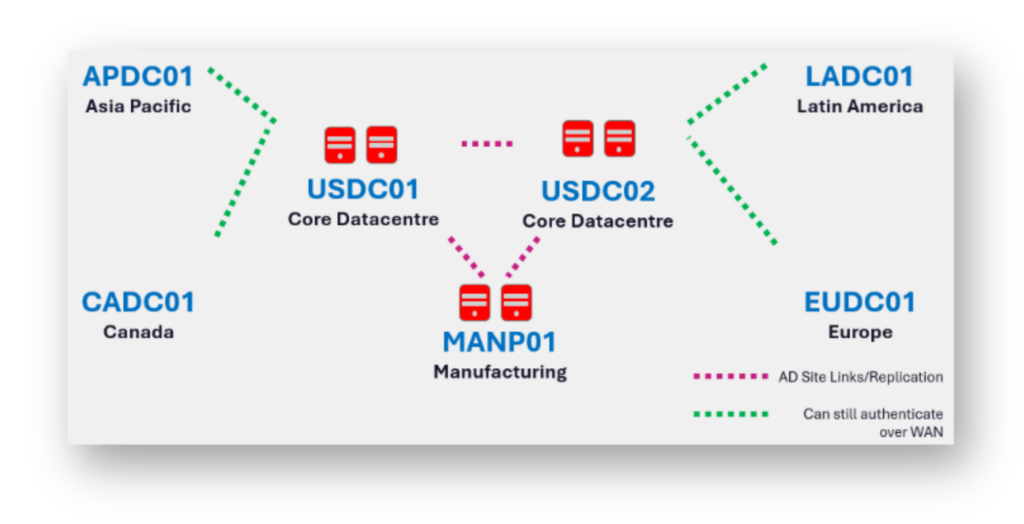
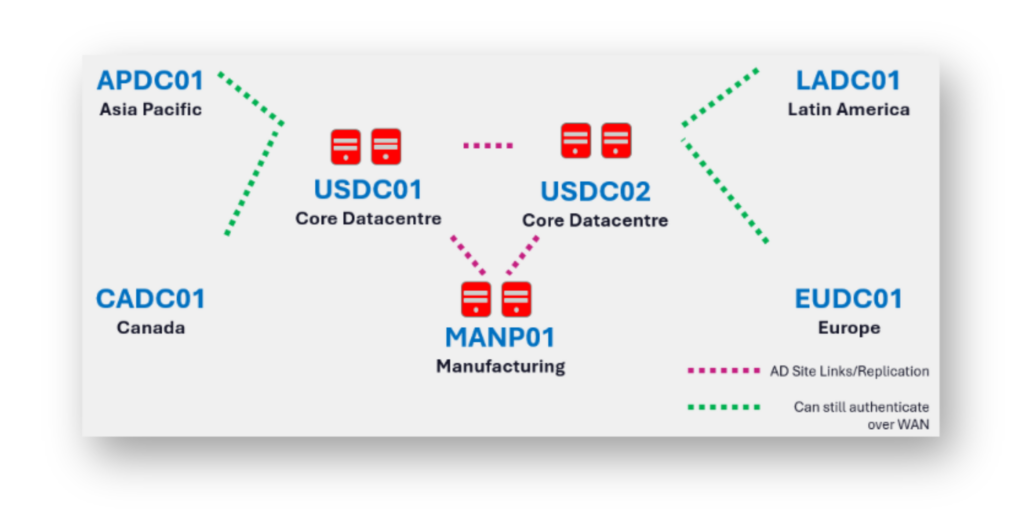
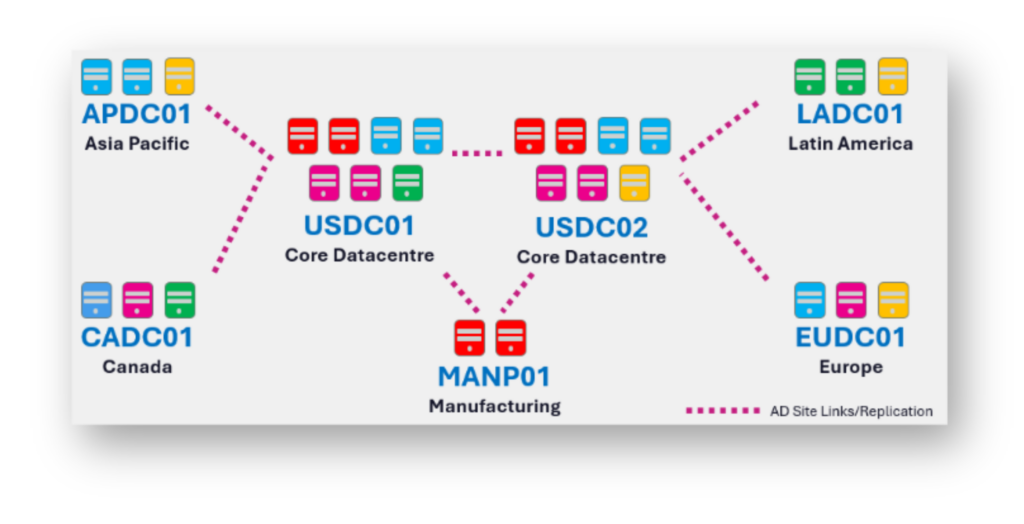
The identity team determined that two domain controllers (DCs) at each primary location were required to support post-breach forensics, remediation efforts, and the restoration of initial authentication services (Figure 3). Once global network connectivity was re-established, regional locations could continue to authenticate across the WAN.
People: The human element of the MVC
During the planning phase, it immediately became apparent to Megakorp that people would play the most important role in any recovery effort. As part of both the identity recovery MVC plan and the broader enterprise MVC strategy, Megakorp mapped out who would be responsible, accountable, consulted, and informed (RACI) for each stage of the recovery process. By doing so, the company ensured that when a task required execution, there was no ambiguity as to who was responsible.
Flexibility and fault tolerance during recovery
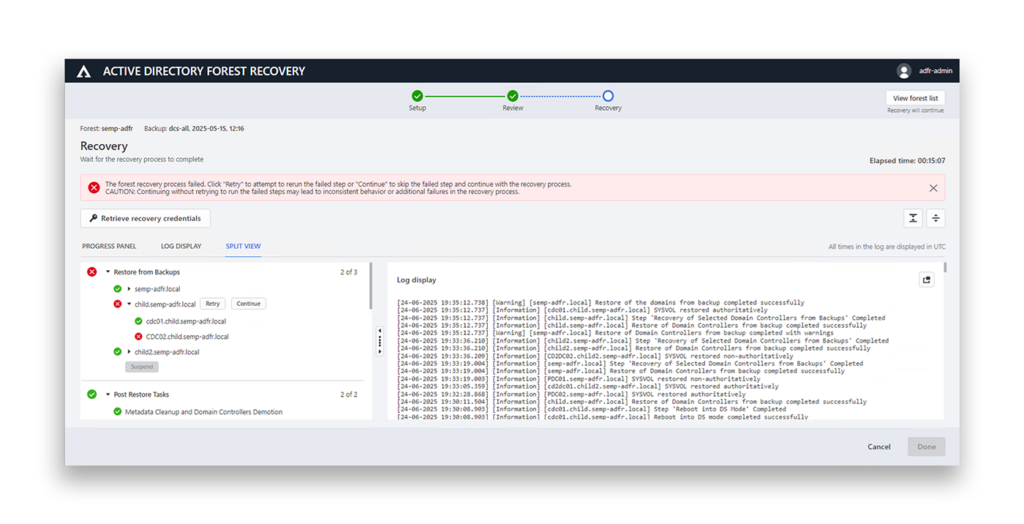
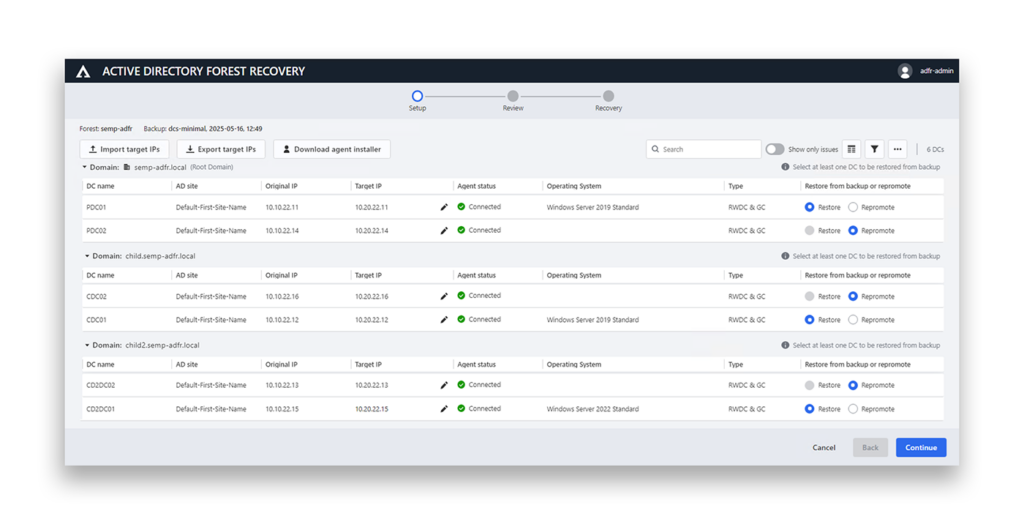
As part of the overall identity recovery strategy, Megakorp was concerned that the failure of a single DC during recovery could cause the entire process to stall. To mitigate this risk, Megakorp mandated that its identity recovery process must be both fault tolerant and flexible (Figure 4).
Megakorp also recognized that legal requirements imposed by internal or external parties, such as law enforcement, could prevent the reuse of its original hardware. Therefore, its MVC recovery plan needed to support the restoration of identity services across different platforms; for example, from physical servers to virtual machines or even from one cloud identity provider to another.
It also became clear that the company’s existing IP address space might not be usable during or after recovery. As a result, the recovery plan needed to account for scenarios in which infrastructure would need to be rebuilt using new network addressing (Figure 5).
Why Megakorp avoided system state and bare metal recovery
One of the primary concerns Megakorp faced was understanding how to recover in a safe and malware-free manner. The team quickly recognized that traditional recovery methods such as system state and bare metal recovery (BMR) could introduce the risk of restoring compromised operating systems or reintroducing malware into the environment.
Megakorp was also concerned about how far back backups would need to be restored to confidently avoid reinfection.
Due to these concerns, Megakorp decided that the recovery of its identity infrastructure must support rebuilding DCs on clean operating systems, ensuring a malware-free recovery process. Recovering the identity MVC and potentially being re-compromised due to operating system–based persistence was simply unacceptable.
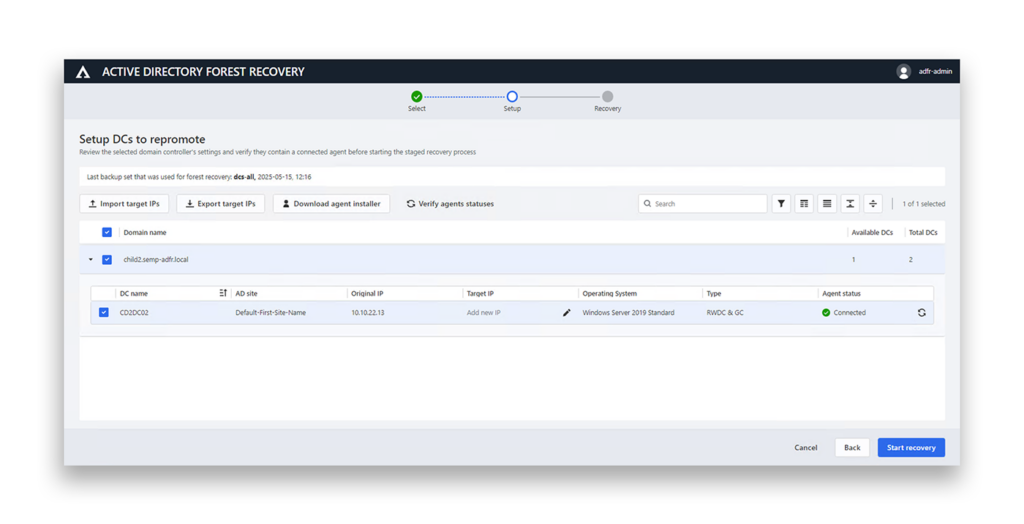
Beyond the MVC: A staged recovery approach
Recognizing that restoring the MVC represents only the initial phase of recovery, Megakorp understood that additional critical applications, infrastructure, and workloads would gradually return to service.
To support this, the organization planned for the staged reintroduction of additional identity infrastructure as time and resources allowed (Figure 6).
Worst. Day. Ever.
All this planning existed for one reason: the day Megakorp hoped would never arrive.
And then it happened.
One day, Megakorp faced its worst-case scenario: a destructive ransomware attack that crippled large parts of its IT infrastructure. Automation on the shop floor stopped working, employees could not log in, systems went offline, and things began to fail.
But there was a plan. A tried and tested plan.
After containment and initial post-breach forensic analysis, Megakorp activated its Minimum Viable Company recovery strategy.
As part of this planning, Megakorp mandated that the identity recovery platform must operate independently of the production environment. This ensured that recovery capabilities would remain available even if the primary infrastructure had been fully compromised.
The company spun up its isolated recovery environment (IRE). Six blank servers were provisioned, and Semperis Active Directory Forest Recovery (ADFR) recovery agents were installed and brought online.
Using ADFR, the team swiftly restored the six DCs that formed the identity MVC.
Once the identity MVC was restored and available, post-breach containment and Identity Forensics and Incident Response (IFIR) activities began. Systems were hardened and administrative tiering was introduced.
At this point, the MVC as it pertained to identity had been successfully recovered (Figure 7). Because the organization had prioritized identity resilience, it was able to restore the identity services that underpin authentication, authorization, and auditing (AAA) within its agreed recovery time objective (RTO). This action enabled critical authentication workloads to resume and enabled the broader Minimum Viable Company to begin operating again.
Business resilience: From survival to stability
With the MVC restored, secured, and hardened, and the stress levels of stakeholders beginning to ease, Megakorp was able to gradually reintroduce additional infrastructure to support increasing AAA workloads.
As a global enterprise, not every region was able to restore infrastructure at the same pace. As Asia Pacific, Canada, and Europe brought infrastructure back online, Megakorp recovered additional DCs to support regional authentication services.
At this stage, most of Megakorp’s applications, users, and systems were once again able to authenticate locally. Systems in Latin America continued to authenticate globally over the WAN, thanks to the fault tolerant nature of Active Directory (Figure 8).
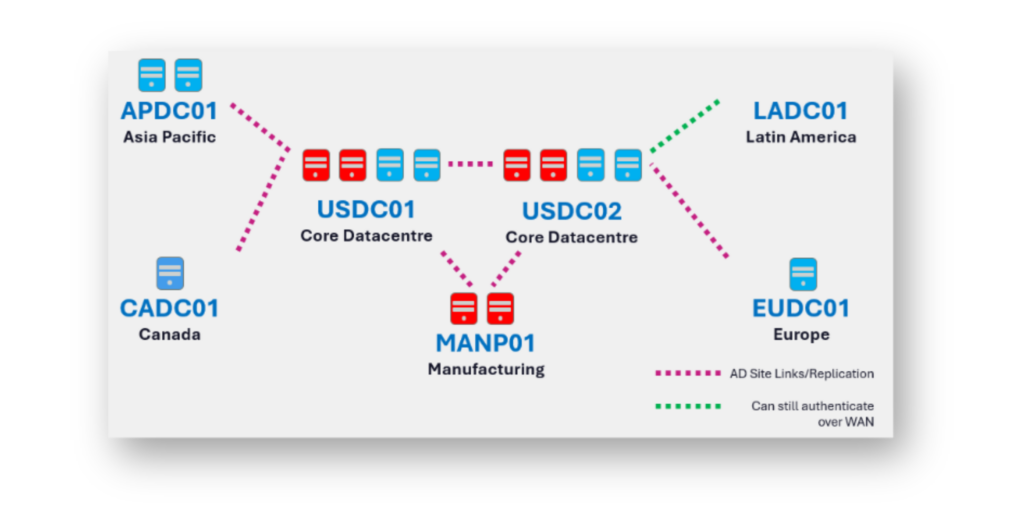
After several stages of infrastructure deployment and procurement, the global Active Directory environment midway through the recovery process resembled the one illustrated in Figure 9.
Once the recovery process was complete, the fully restored identity infrastructure was as shown in Figure 10. During recovery, Megakorp made the conscious decision to reduce the number of DCs globally, and the final environment reflects this updated architecture.
At this point, global operations were fully restored, with applications, users, and systems across all regions able to authenticate locally.
Building the wider MVC on a foundation of identity
With identity stabilized and authentication restored, Megakorp could now safely begin recovering the wider enterprise environment.
As time and resources allowed, the company gradually brought the remainder of the environment back online. The entire recovery process followed the stages outlined in Figure 11.
After the dust settled
With Megakorp now on the other side of recovery and operations returned to normal, new policies and processes were implemented to reduce the likelihood of a similar occurrence.
The recovery reinforced an important lesson:
- Identity must be restored first.
- Authentication should follow.
- Systems can then be returned.
- Applications can be resumed.
- The business will survive.
The organization also incorporated the lessons learned during this incident into its recovery procedures, ensuring that if such an event were to happen again, they would be even more efficient and better positioned to recover.
Megakorp’s worst day proved one thing: When identity survives, so does the business.
To learn how Semperis can help you safeguard the recovery of your MVC (and your business), schedule a demo.
Additional resources
- Rethinking Cyber Crisis Management: Why Plans Fail
- The Missing Layer in Cyber Incident Response: Crisis Orchestration
- 5 Keys to Fault-Tolerant Active Directory Recovery
- Identity Recovery & Crisis Management: Inseparable for Incident Response
- Facilitating Cyber Crisis Tabletops: Front-Line Leadership Insights
- Beyond Defense: AD Recovery and Business Resilience
