- The modern identity landscape
- MVC resilience beyond on-prem: The cloud protection conundrum
- These are our identities, so we must protect them
- Privileged access for backup solutions? Not at the expense of security
- Choosing well: Cloud identity protection and recovery for cyber resilience
- Crisis management challenge: How to secure communications in an insecure environment
- Ready when it matters: Secure crisis communications
- Applying identity insights before the next breach
- Further reading
An essential part of planning for cyber incident response and recovery is determining your Minimum Viable Company (MVC). That means discovering what services and functions are absolutely essential to keep your organization viable and operating in a crisis.
The identity system is the foundation for all those essential MVC elements. And for most modern organizations, identity is not contained within on-premises Active Directory but extends across the cloud through Microsoft Entra ID and other cloud identity providers.
Consider the recovery experience of the fictitious company Megakorp, which I wrote about in my previous blog The Minimum Viable Company: Why True Cyber Resilience Starts with Identity. In that installment, we followed Megakorp on its journey to cyber resilience, exploring the development and realization of its MVC—and what happened on its worst day, when it was hit with an on-premises ransomware attack.
By preparing for resilience long before a breach occurred, the organization was able to recover rapidly, safely, and securely.
However, although Megakorp was able to recover as designed—within the expected recovery time objective (RTO) and maintaining customer trust—this outcome was partly attributable to the fact that the breach was limited to on-premises systems.
What happens when your MVC extends into the cloud?
In the aftermath of Megakorp’s event, it became clear that gaps existed in the organization’s crisis management approach, and that achieving true resilience required addressing those gaps.
The modern identity landscape
Let’s revisit Megakorp’s modern identity landscape and its approach to cloud-based applications.
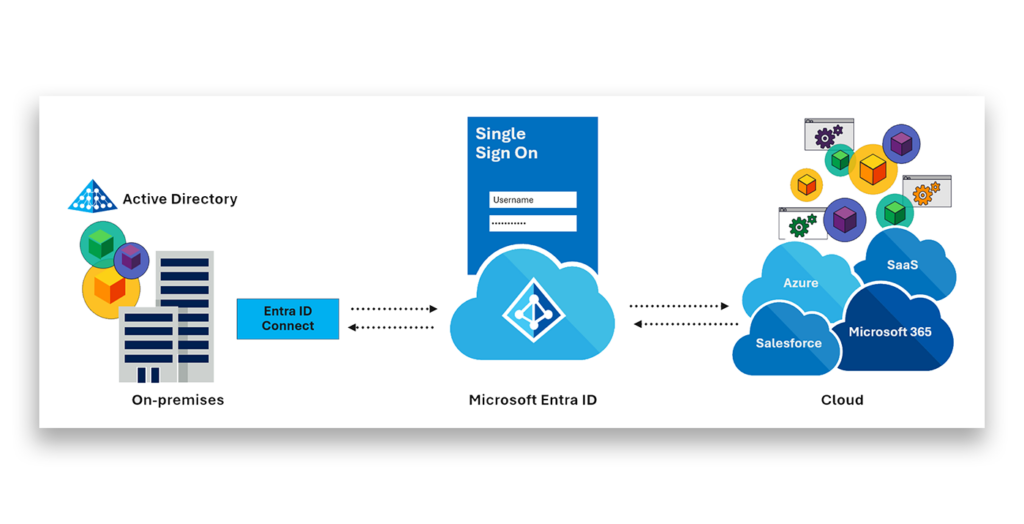
Like many enterprises, Megakorp extends on-premises identities from Active Directory into its cloud-based identity provider, Entra ID. From there, employees access enterprise applications such as Microsoft 365, Workday, Monday.com, and Salesforce, enabling modern business productivity.
This architecture extends trust boundaries beyond traditional on-premises control—and this is where the first gap immediately becomes apparent.
MVC resilience beyond on-prem: The cloud protection conundrum
After Megakorp contained its breach to on-premises systems and recovered to a trusted state, the disaster recovery team began to assess the potential impact of an attacker transitioning from on-premises control to cloud control.
The team quickly determined that cloud identities, together with their associated configurations, were critical to business operations. If cloud applications were deleted, blocked, or modified, how would Megakorp ensure that critical components could be designed, manufactured, and shipped? How would invoices be sent, received, or processed?
Responding to those findings, the board mandated that cloud identities must also be included in the defined MVC and protected in alignment with the approach the company takes to prepare for on-premises cyber resilience.
To provide that coverage, the organization needed to determine:
- The scope of their responsibility for cloud identity security
- How to handle access control for their chosen identity protection solution
- Which cloud identity protection and recovery solution to choose
These are our identities, so we must protect them
Megakorp recognized that cloud identities were their identities and therefore required the same level of protection as identities in on-premises AD.
The Microsoft shared responsibility model confirms this position explicitly. It’s not a matter of interpretation.
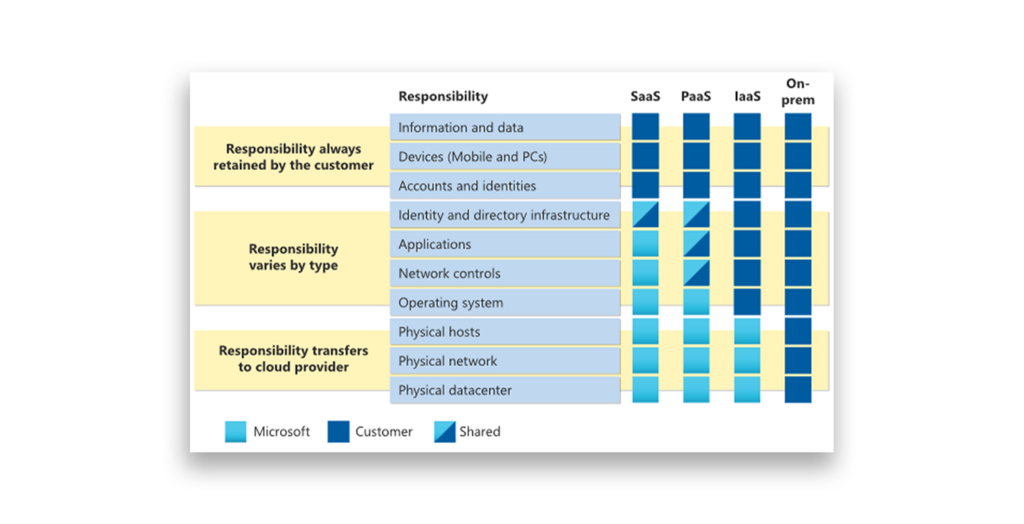
The Microsoft Shared responsibility in the cloud documentation also lays out the responsibility clearly, stating:
…For all cloud deployment types, you own your data and identities. You’re responsible for protecting the security of your data and identities, on-premises resources, and the cloud components you control…
With this delineation in mind, Megakorp adopted the approach that had proved effective for on-premises identities, setting the expectation that cloud identities be protected with the same rigor.
Privileged access for backup solutions? Not at the expense of security
During the evaluation of cloud-based identity protection, two contrasting approaches to access control emerged:
- Granting the backup solution broad administrative privileges across Entra ID, or
- Adhering to the principle of least privilege, delegating only the permissions necessary to protect critical identities and configurations.
In line with their approach for on-premises resilience, Megakorp conducted detailed research into how identity environments are being compromised and controlled.
This analysis identified several high-impact, high-visibility breaches in which application compromise had played a central role. In many cases, applications designed to protect or enable organizations had instead been leveraged as attack vectors.
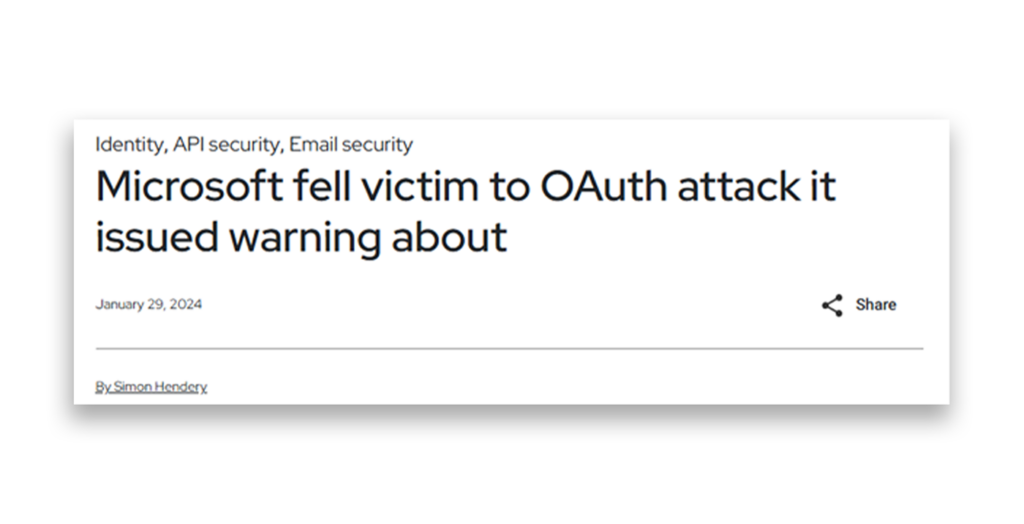
Given these findings, Megakorp made a decision: They would enforce the principle of least privilege, granting only the permissions explicitly required to protect the environment.
Choosing well: Cloud identity protection and recovery for cyber resilience
Megakorp began evaluating solutions capable of delivering secure and resilient cloud identity protection.
Any selected solution would need to:
- Adhere to the principle of least privilege
- Avoid introducing additional risk
- Support controlled recovery of critical identities and configurations
- Orchestrate recovery operations using trusted employee accounts
- Support recovery with additional controls such as multi-factor authentication, role-based access control (RBAC) and accurate Entra ID auditing
- Ensure a secure and controlled recovery process
Following the evaluation, Megakorp selected Semperis Disaster Recovery for Entra Tenant (DRET) because it aligned with these requirements for identity protection and recovery.
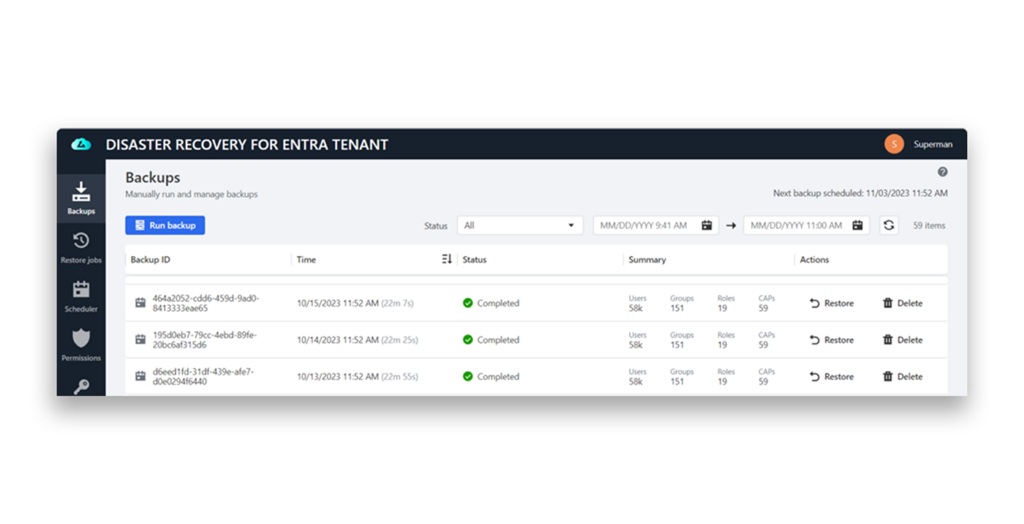
With on-premises and cloud identities and configurations now protected, one significant challenge remained: the loss of trust in the primary collaboration platform during an incident.
Crisis management challenge: How to secure communications in an insecure environment
During their ransomware attack, Megakorp quickly learned that securing communications in an untrusted environment was extremely challenging. The board had no assurance that discussions, legal conversations, and recovery plans were not being intercepted by threat actors.
Initial communications proved highly problematic. In an attempt to coordinate, the teams pivoted to using multiple instant messaging platforms, leveraging LinkedIn to obtain personal contact details such as telephone numbers and email addresses of key employees as they struggled to establish some form of out-of-band communication.
Documentation sharing and collaboration was severely limited. Team calls were conducted ad hoc via Zoom, while legal transcripts and recovery documentation were stored locally on employee devices.
Critically, the MVC recovery plan was accessible only because a key employee happened to have a locally saved copy on their work laptop before the breach.
Ready when it matters: Secure crisis communications
When identity is the control plane, communications platforms become part of the blast radius.
To address this challenge, Megakorp identified the need for a secure, out-of-band communications platform capable of operating independently of any compromised environment and where legal privilege could be applied.
The board mandated that any such solution must:
- Ensure confidentiality and integrity of communications, data, and documentation
- Include a mechanism for recording and transcribing activities during incidents
- Provide a single, trusted platform for collaboration and communication before, during, and after an incident
Having implemented Semperis Active Directory Forest Recovery (ADFR) and committed to implementing DRET, Megakorp determined that adopting Ready 1—a platform purpose-built for cyber crisis management—was a logical extension of its resilience strategy.
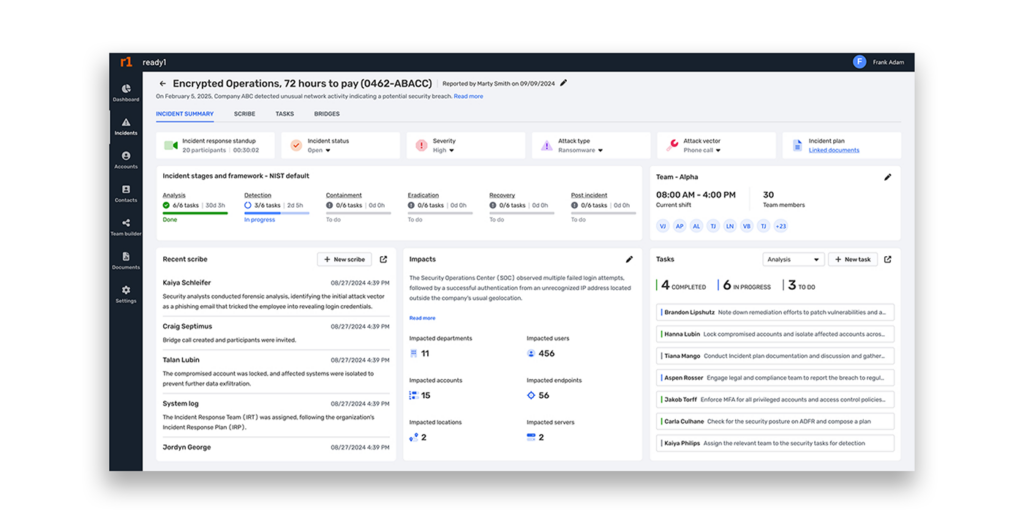
Adopting Ready1 enabled Megakorp to address some of the most significant challenges that the ransomware incident exposed.
- Before an incident, teams could ensure playbooks, runbooks, critical technical and operational documentation, and contact details were readily available.
- During an incident, Ready1 would provide secure out of band communications, shared and protected document storage, and legal scribe and redaction capabilities.
- Post incident, Ready1 would ensure that all identified gaps and learned lessons are consolidated into a single source of truth, providing transparency, preventing duplication, and enabling clear ownership by assigning each action to the appropriate individual or team.
Applying identity insights before the next breach
Megakorp’s journey so far has shown them that recovery and secure communications are critical for resilience. However, they are not sufficient on their own—and the company’s journey is not over.
Their next step toward true resilience demands establishing deeper visibility and understanding of activity within the identity environment as well as identifying vulnerabilities before they can be exploited.
Because resilience is not a destination; it’s all about the journey.
Further reading
- Minimum Viable Company: True Cyber Resilience Starts with Identity
- Understanding Your Identity Security Posture | Hybrid Identity Protection
- Hardening Entra ID Recovery and Identity Security Resilience
- The Missing Layer in Cyber Incident Response: Crisis Orchestration
- Identity Recovery & Crisis Management: Inseparable for Incident Response
- Entra ID Disaster Recovery
- Ready1 Cyber Resilience and Crisis Management Platform – Semperis
