I’ve spent years working with organizations to prepare for their worst day—building risk management programs, quantifying potential impact, and helping leaders understand what matters most to the business.
Yet one thing continues to stand out: many organizations are still woefully unprepared to manage a real cyber crisis.
- Not because they lack effort.
- Not because they lack talent.
- But because they lack actionable guidance for making decisions under pressure.
Today, the cybersecurity industry measures the presence of plans—not the effectiveness of response.
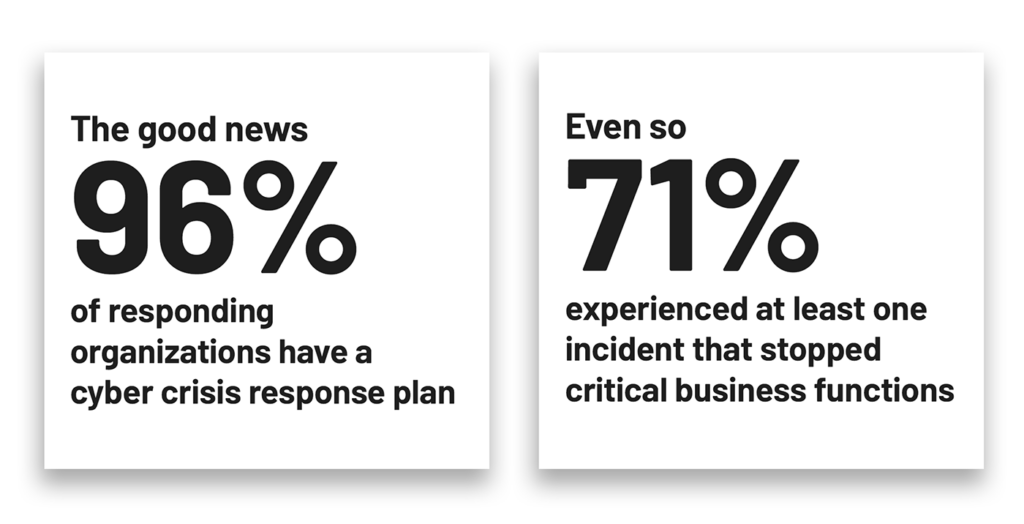
Most organizations believe they are prepared because they have incident response plans, playbooks, and tabletop exercises. But these artifacts often fail when faced with real-world complexity.
Why? Because they attempt to script the unscriptable.
True cyber crisis preparedness doesn’t come from more documentation. It comes from clarity around business priorities and decision authority.
The industry measures the wrong thing
This isn’t a new problem, but industry frameworks continue to reinforce a compliance-driven mindset.
Assessments commonly ask:
- Do you have a response plan?
- Do you maintain playbooks?
- Do you conduct tabletop exercises?
If the answer is yes, the requirement is met. The box is checked. The organization is considered prepared.
But for comprehensive cyber crisis management, organizations rarely ask the questions that matter most:
- Do leaders know how to prioritize business operations during a crisis?
- Do teams understand the financial and operational impact of system failure?
- Do responders know who has authority to make critical decisions?
- Can the organization function when the scenario doesn’t match the playbook?
By measuring the wrong things, we create a dangerous gap—one that produces confidence on paper while leaving organizations operationally fragile during real events.
The myth of the perfect cyber crisis playbook
Another common source of confusion is the way we use the terms runbook and playbook interchangeably, even though they serve very different purposes. That confusion alone can create gaps in preparedness.
Runbooks are tactical execution guides. They provide step-by-step instructions for performing a specific technical task. They are designed for speed, consistency, and repeatability — and they work well when the situation is predictable.
Playbooks, on the other hand, operate at a higher level. They provide guidance for responding to a category of incident, often including coordination steps, communication guidance, and escalation paths across teams.
Both are valuable. But both share the same limitation: they assume the crisis will unfold according to a known scenario.
Real cyber crises rarely do.
A ransomware event may encompass identity compromise, system outages, data exfiltration, regulatory reporting, customer impact, legal review, and law enforcement involvement—all at the same time.
No playbook can anticipate that level of cascading complexity.
What I see in practice is that teams abandon the playbook within hours and rely on experience, intuition, and improvisation.
That is not a failure of the responders. It is a failure of the model.
We have trained teams to follow scripts, but we have not equipped them to make decisions when the script breaks.
Runbooks and playbooks remain important tools, but they are not designed to solve the hardest problem in cyber crisis management: coordinating high-stakes decisions across the business when the situation does not match a predefined scenario.
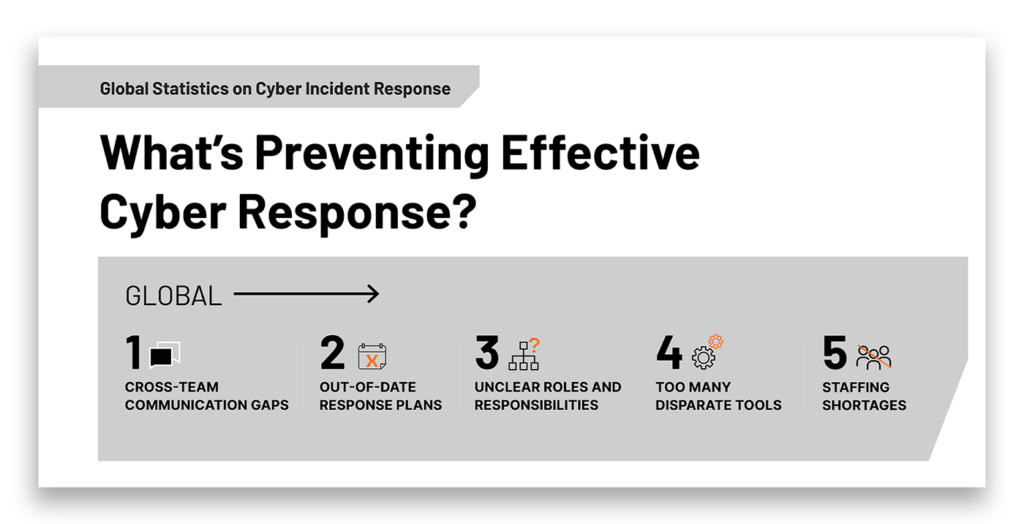
The real problem during a cyber crisis: Decision paralysis
In most cyber crises, the biggest delays are not technical. They are decision-based.
- Who declares a crisis?
- Who can shut down systems?
- Who approves customer communication?
- Who decides what gets restored first?
- Who accepts risk when there is no perfect option?
Uncertainty around authority can stall even the most critical actions.
To make effective decisions under pressure, responders need more than a plan. They need a decision framework.
An effective crisis decision framework should define three things:
- What matters most to the business
Clear agreement on critical operations, priorities, and acceptable tradeoffs - Where critical decisions occur
Mapping the key decision points that arise during different types of incidents - Who has authority at those points
Defined decision ownership that allows teams to act without delay
When these elements are defined in advance, responders can move faster, act with confidence, and make decisions that remain defensible after the crisis.
Without them, even well-trained teams hesitate. And hesitation is costly.
Testing the right things
If runbooks and playbooks cannot capture the complexity of a real crisis, then cyber crisis simulation exercises must evolve as well.
Too many tabletop exercises validate the plan instead of challenging it.
Effective exercises should focus on questions like:
- Do leaders truly agree on business priorities?
- Do decision-makers understand tradeoffs?
- Can teams coordinate under pressure?
- Can the organization function with incomplete or conflicting information?
Exercises should simulate:
- Cascading impacts
- Uncertain or changing information
- Executive-level decision points
- Cross-functional coordination challenges
The goal is not to prove the plan works. The goal is to prove the organization can adapt when the plan doesn’t.
Real preparedness comes from building the ability to pivot while staying aligned to what matters most.
The path forward: Start with a North Star
If we accept that we cannot script every incident, then cyber crisis management must start somewhere else.
It starts with alignment. Ask your leadership team a simple question:
What matters most to this business?
I often refer to this as the organization’s North Star.
When teams understand the North Star, they can make decisions even when the situation is unclear. They can ask:
- Does this action protect our most critical operations?
- Does this decision align with our stakeholder priorities?
- Does this move get us closer to recovery where it matters most?
If the answer is yes, the decision is defensible. If the answer is no, it should not be the priority during a crisis.
The North Star does not replace runbooks or playbooks. It makes them usable.
Because when the script fails—and it will—the organization still knows how to decide.
And in a real cyber crisis, the ability to decide is what separates chaos from control.
Related resources
- The Missing Layer in Cyber Incident Response: Crisis Orchestration
- The Modern Model for Cyber Crisis Management
- Identity Recovery & Crisis Management: Inseparable for Incident Response
- The State of Enterprise Cyber Crisis Readiness
- Facilitating Cyber Crisis Tabletops: Front-Line Leadership Insights
- Tech Talk From Chaos to Control: Rethinking Cyber Crisis Management
- Redefining Cyber Crisis Management
- Ready1 Cyber Resilience and Crisis Management Platform



