Featured posts
- Eitan Bloch | Semperis Product Manager
- Apr 30, 2024
Categories
Latest posts
Categories
Active Directory Backup & Recovery
Active Directory Attacks: Why Cyber Threats Target AD
- Darren Mar-Elia
- Feb 21, 2024
[Updated February 21, 2024; originally published December 14, 2017] Active Directory is the most critical identity system for most enterprises. The problem is that in the two-plus decades since Active…
A Swift Ransomware Response is the Path to Business Resiliency
- Mickey Bresman
- Dec 22, 2023
Cyberattacks on business systems—including hybrid identity systems—continue to make headlines, including recent breaches targeting healthcare company Henry Schein and hospitality conglomerate MGM Resorts. Apart from these well-publicized attacks, the Semperis…
How Can K-12 Schools Defend Against Ransomware?
- Jared Vichengrad
- Feb 02, 2023
The cybersecurity challenges in the government and education space are nothing new. Such challenges soared with COVID and continue today. Unfortunately, the cyber defense of mission-critical government and education services…
Active Directory Security
How to Defend Against SID History Injection
- Daniel Petri
- May 03, 2024
Security Identifier (SID) History injection is a sophisticated cyberattack vector that targets Windows Active Directory environments. This attack exploits the SID History attribute, which is intended to maintain user access…
Identity Attack Watch: AD Security News, April 2024
- Semperis Research Team
- May 01, 2024
As cyberattacks targeting Active Directory continue to rise, AD security, identity, and IT teams face mounting pressure to monitor the evolving AD-focused threat landscape. To assist IT professionals in comprehending…
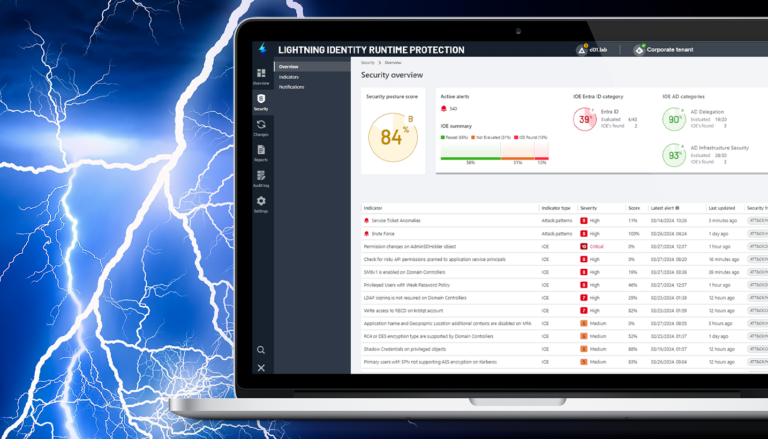
Introducing Lightning Identity Runtime Protection: ML-powered detection of the most successful identity attack patterns
- Eitan Bloch | Semperis Product Manager
- Apr 30, 2024
Many cyberattacks go undetected until the damage is done, despite organizations’ efforts to prevent them. And many successful identity attacks use the same tried-and-true techniques that have worked for years,…
AD Security 101
How to Defend Against SID History Injection
- Daniel Petri
- May 03, 2024
Security Identifier (SID) History injection is a sophisticated cyberattack vector that targets Windows Active Directory environments. This attack exploits the SID History attribute, which is intended to maintain user access…
LDAP Injection Attack Defense: AD Security 101
- Daniel Petri
- Mar 06, 2024
LDAP injection represents a formidable cyberattack vector, targeting the authentication and authorization mechanisms within your Active Directory environment. By exploiting improper input validation, attackers can manipulate LDAP statements and potentially…
Pass the Hash Attack Defense: AD Security 101
- Daniel Petri
- Jan 18, 2024
Many Active Directory attacks begin with a stolen password. However, a Pass the Hash attack takes a different approach. In this example of credential theft, threat actors instead steal a…
Community Tools
Purple Knight Scoring Improves Understanding of Identity System Security Vulnerabilities
- Ran Harel
- Dec 13, 2023
Our latest Purple Knight (PK) v4.2 release introduces fundamental changes, particularly concerning the new scoring calculation. Changing from a broader approach that considered all indicators, we’ve now zeroed in on…
Semperis Offers New Protection Against Okta Breaches
- Semperis Research Team
- Aug 30, 2023
In an ever-evolving digital landscape, organizations rely on robust identity protection solutions to safeguard sensitive data and maintain secure operations. For most enterprise businesses, that means protecting Active Directory and…
AD Monitoring: AD Security 101
- Daniel Petri
- Mar 09, 2023
An unmanaged Active Directory (AD) can have a profound impact on your operations, leading to downtime and increasing your vulnerability to network security threats. AD monitoring can provide insights you…
Directory Modernization
Security-Centric Active Directory Migration and Consolidation
- Michael Masciulli
- Oct 17, 2023
Enterprise organizations with legacy Active Directory (AD) environments have a security problem. Their AD infrastructure has likely degraded over time and now harbors multiple security vulnerabilities because of inefficient architecture,…
Active Directory Migration: 15 Steps to Success
- Daniel Petri
- Apr 18, 2023
Active Directory (AD) migration projects can be challenging and complex. Such projects involve the migration of users, groups, computers, and applications from one AD domain or forest to another. Careful…
Why AD Modernization Is Critical to Your Cybersecurity Program
- Mickey Bresman
- Apr 03, 2023
Active Directory (AD) is the core identity store for many organizations. As such, AD has also become a major target for bad actors. If attackers gain access to AD, they…
From the Front Lines
LockBit, Law Enforcement, and You
- Mickey Bresman
- Feb 28, 2024
Another day, another installment in the LockBit saga. The latest development in the never-ending story of cyber-criminal gangs versus law enforcement agencies is nearly worthy of its own TV series….
Active Directory Attacks: Why Cyber Threats Target AD
- Darren Mar-Elia
- Feb 21, 2024
[Updated February 21, 2024; originally published December 14, 2017] Active Directory is the most critical identity system for most enterprises. The problem is that in the two-plus decades since Active…
Identity Attack Watch: AD Security News, January 2024
- Semperis Research Team
- Jan 31, 2024
As cyberattacks targeting Active Directory continue to rise, AD security, identity, and IT teams face mounting pressure to monitor the evolving AD-focused threat landscape. To assist IT professionals in comprehending…
Hybrid Identity Protection
Accelerate AD and Entra ID Protection from Cyber Threats
- Eitan Bloch | Semperis Product Manager
- Apr 19, 2024
How secure is your hybrid identity environment? Since the discovery of the SolarWinds breach in December 2020, cyberattacks that start in the cloud environment—Entra ID for most organizations—and move to…
Meet Silver SAML: Golden SAML in the Cloud
- Tomer Nahum and Eric Woodruff
- Feb 29, 2024
Key findings Golden SAML is a known attack technique discovered by CyberArk and published by Shaked Reiner. For years, Golden SAML has been known for its extraction of signing certificates…
How to Defend Against an Overpass the Hash Attack
- Daniel Petri
- Feb 09, 2024
In the constantly evolving landscape of cyber threats, the Overpass the Hash attack is a potent vector. Leveraging the NTLM authentication protocol, this attack enables adversaries to bypass the need…
Identity Attack Catalog
How to Defend Against SID History Injection
- Daniel Petri
- May 03, 2024
Security Identifier (SID) History injection is a sophisticated cyberattack vector that targets Windows Active Directory environments. This attack exploits the SID History attribute, which is intended to maintain user access…
LDAP Injection Attack Defense: AD Security 101
- Daniel Petri
- Mar 06, 2024
LDAP injection represents a formidable cyberattack vector, targeting the authentication and authorization mechanisms within your Active Directory environment. By exploiting improper input validation, attackers can manipulate LDAP statements and potentially…
How to Defend Against an Overpass the Hash Attack
- Daniel Petri
- Feb 09, 2024
In the constantly evolving landscape of cyber threats, the Overpass the Hash attack is a potent vector. Leveraging the NTLM authentication protocol, this attack enables adversaries to bypass the need…
Identity Threat Detection & Response
How to Defend Against SID History Injection
- Daniel Petri
- May 03, 2024
Security Identifier (SID) History injection is a sophisticated cyberattack vector that targets Windows Active Directory environments. This attack exploits the SID History attribute, which is intended to maintain user access…
Accelerate AD and Entra ID Protection from Cyber Threats
- Eitan Bloch | Semperis Product Manager
- Apr 19, 2024
How secure is your hybrid identity environment? Since the discovery of the SolarWinds breach in December 2020, cyberattacks that start in the cloud environment—Entra ID for most organizations—and move to…
LDAP Injection Attack Defense: AD Security 101
- Daniel Petri
- Mar 06, 2024
LDAP injection represents a formidable cyberattack vector, targeting the authentication and authorization mechanisms within your Active Directory environment. By exploiting improper input validation, attackers can manipulate LDAP statements and potentially…
Our Mission: Be a Force for Good
Duns 100 Ranks Semperis in Top 15 to Work For
- Yarden Gur
- Nov 28, 2022
This month marked two milestones for Semperis. First, Deloitte recognized the company as one of the 100 fastest growing technology companies in North America and (for the third consecutive year)…
What It Means to be a Mission-Driven Company
- Mickey Bresman
- May 18, 2022
On behalf of the entire team, I’m excited to share that Semperis has been named to Inc.’s 2022 list of Best Workplaces. This annual list honors workplaces that are ranked…
Hybrid Identity Protection: IDPro Founder Ian Glazer
- Sean Deuby
- May 11, 2022
You won’t want to miss the newest episode of the Hybrid Identity Podcast (HIP)! In this session, I have the pleasure of talking with IDPro founder and Salesforce Senior VP…
Purple Knight
Purple Knight Scoring Improves Understanding of Identity System Security Vulnerabilities
- Ran Harel
- Dec 13, 2023
Our latest Purple Knight (PK) v4.2 release introduces fundamental changes, particularly concerning the new scoring calculation. Changing from a broader approach that considered all indicators, we’ve now zeroed in on…
Semperis Offers New Protection Against Okta Breaches
- Semperis Research Team
- Aug 30, 2023
In an ever-evolving digital landscape, organizations rely on robust identity protection solutions to safeguard sensitive data and maintain secure operations. For most enterprise businesses, that means protecting Active Directory and…
How to Prevent a Man-in-the-Middle Attack: AD Security 101
- Daniel Petri
- Jul 13, 2023
A man-in-the-middle attack, also known as an MitM attack, is a form of eavesdropping in an attempt to steal sensitive data, such as user credentials. These attacks can pose a…
The CISO’s Perspective
Top 3 Identity-Based Attack Trends to Watch in 2024
- Semperis
- Jan 02, 2024
Each year, the total number of cyberattacks and cost of ransomware-related damage increases globally. Microsoft recently reported that attempted password attacks have soared “from around 3 billion per month to…
5 Essential ITDR Steps CISOs Must Know
- Semperis Team
- Jan 26, 2023
Just as the impact of cyberattacks is not confined to the IT department, the role of the CISO has expanded beyond the security team. With organizations and analysts now acknowledging…
How to Build a Strong ITDR Strategy
- Sean Deuby
- Jan 17, 2023
How do you begin to build a strong Identity Threat Detection and Response (ITDR) strategy? It begins with an understanding of your unique identity environment, says Maarten Goet, Director for…
Threat Research
How to Defend Against SID History Injection
- Daniel Petri
- May 03, 2024
Security Identifier (SID) History injection is a sophisticated cyberattack vector that targets Windows Active Directory environments. This attack exploits the SID History attribute, which is intended to maintain user access…
Meet Silver SAML: Golden SAML in the Cloud
- Tomer Nahum and Eric Woodruff
- Feb 29, 2024
Key findings Golden SAML is a known attack technique discovered by CyberArk and published by Shaked Reiner. For years, Golden SAML has been known for its extraction of signing certificates…
How to Defend Against a Pass the Ticket Attack: AD Security 101
- Daniel Petri
- Jan 11, 2024
Any organization that relies on Kerberos authentication—the primary authentication method in Active Directory environments—is potentially vulnerable to a Pass the Ticket attack. Organizations that do not regularly patch their systems,…
Uncategorized
AD Security 101: Lock Down Risky User Rights
- Daniel Petri
- Jun 16, 2023
In Active Directory (AD) environments, you can use Group Policy Objects (GPOs) to configure user rights. By using GPOs, you can easily enforce consistent user rights policies across all computers…
AD security resources
Stay informed. Get the latest news and resources on identity threat detection and response (ITDR), hybrid Active Directory (AD) security, and cyber resilience, brought to you by Semperis experts.