Threat Research
Categories
- Active Directory Backup & Recovery (69)
- Active Directory Security (239)
- AD Security 101 (18)
- Community Tools (26)
- Crisis Management (5)
- Directory Modernization (9)
- From the Front Lines (70)
- Hybrid Identity Protection (85)
- Identity Attack Catalog (32)
- Identity Threat Detection & Response (170)
- Our Mission: Be a Force for Good (14)
- Purple Knight (6)
- Semperis University (5)
- The CISO's Perspective (18)
- Threat Research (79)
- Uncategorized (3)

What You Need to Know: Windows Admin Center Remote Privilege Escalation (CVE-2026-26119)
- Andrea Pierini
- Mar 23, 2026
Learn about the discovery of CVE-2026-26119: why it worked and why you shouldn't underestimate authentication reflection.
SyncJacking: Hard Matching Vulnerability Enables Entra ID Account Takeover
- Tomer Nahum
- Jan 13, 2026
Attackers with certain privileges can abuse Entra Connect hard matching synchronization to take over synchronized Entra ID accounts.

nOAuth Abuse Update: Potential Pivot into Microsoft 365
- Eric Woodruff | Chief Identity Architect
- Jan 05, 2026
Additional nOAuth research indicates that the risk of nOAuth abuse still exists and that many organizations are still unaware of this vulnerability.

Exploiting Ghost SPNs and Kerberos Reflection for SMB Server Privilege Elevation
- Andrea Pierini
When misconfigured Service Principal Names (SPNs) and default permissions align, attackers can exploit Kerberos reflection to gain SYSTEM-level access remotely. Even with Microsoft’s security update, Ghost SPNs can still haunt you. Learn why.

EntraGoat Scenario 6: Exploiting Certificate-Based Authentication to Impersonate Global Admin in Entra ID
- Jonathan Elkabas and Tomer Nahum
Editor’s note This scenario is part of a series of examples demonstrating the use of EntraGoat, our Entra ID simulation environment. You can read an overview of EntraGoat and its value here. Certificate Bypass Authority–Root Access Granted EntraGoat Scenario 6 details a privilege escalation technique in Microsoft Entra ID where…
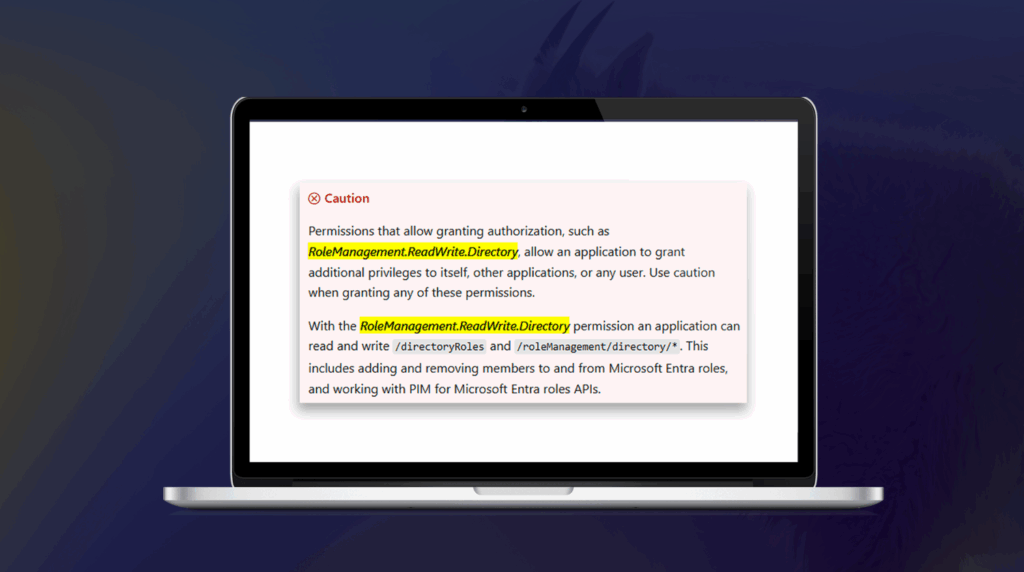
EntraGoat Scenario 2: Exploiting App-Only Graph Permissions in Entra ID
- Jonathan Elkabas and Tomer Nahum
In our second EntraGoat attack scenario, follow the steps from a carelessly leaked certificate to capture the Global Admin password—and full Entra ID compromise.
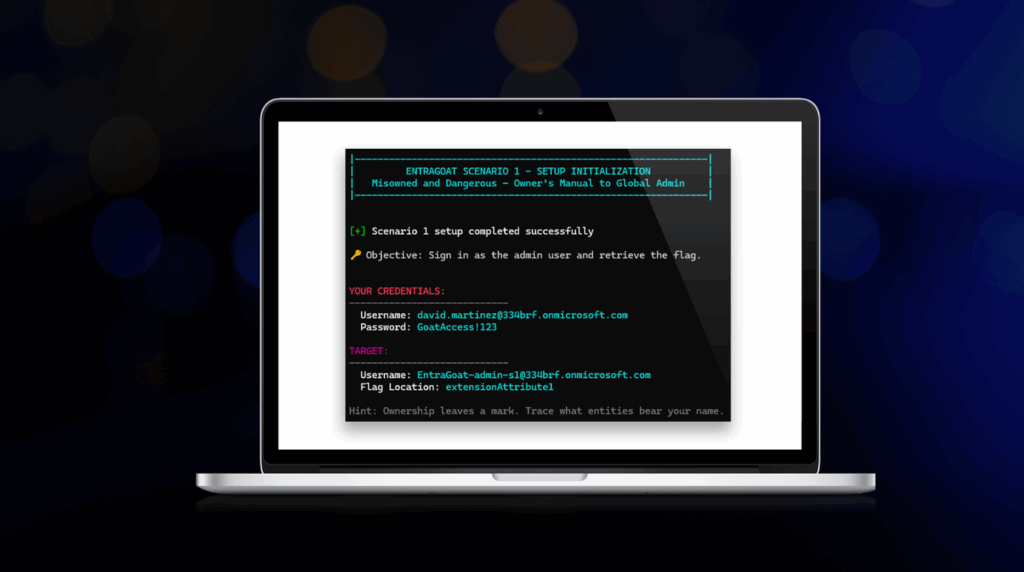
EntraGoat Scenario 1: Service Principal Ownership Abuse in Entra ID
- Jonathan Elkabas and Tomer Nahum
How can a compromised low-privileged user account exploit service principal ownership—and complete an Entra ID tenant takeover? Find out when you dive into EntraGoat Scenario 1.

Getting Started with EntraGoat: Breaking Entra ID the Smart Way
- Jonathan Elkabas and Tomer Nahum
Ready to jump in and get your hooves dirty in EntraGoat? Start here. These quick-start steps will get you into your first attack scenario.



