Active Directory (AD) remains a crucial backbone for enterprise IT environments, centralizing authentication and authorization for users and computers. However, Active Directory’s importance—coupled with its age and the technical debt it often accrues—makes it a primary target for cyberattacks. One common attack technique, called Kerberoasting, exploits the Kerberos authentication protocol and service principal names (SPNs). Here’s a closer look at how Kerberoasting works and how to defend against it.
What is Kerberoasting?
Kerberoasting is a sophisticated attack method. Attackers use Kerberoasting to extract service account credentials. Armed with these credentials, attackers can gain an alarming ability to extensively compromise your network.
The foundation of Kerberoasting is the ability of any authenticated user within an AD domain to request service tickets for any service. These tickets are encrypted using the hash of the service account linked to the queried SPN. The hash—RC4 or DES—is not considered strong by modern standards and thus can be cracked with relative ease.
What is Kerberos?
Kerberos is a network authentication protocol created to offer secure authentication for client-server applications, using secret-key cryptography. The protocol is the default authentication protocol in Active Directory and plays a crucial role in ensuring that users and services can trust one another in a network environment.
Kerberos uses tickets: cryptographic entities that authenticate users or services without repeatedly sending passwords across the network. These tickets serve as the backbone of the Kerberos authentication process.
There are several types of Kerberos tickets:
- Ticket Granting Ticket (TGT): Issued after initial logon, this ticket authorizes the user to request service tickets.
- Service ticket, also known as a Ticket Granting Service (TGS) ticket: This ticket allows users to access specific services.
- Session ticket: After a service ticket is presented to and verified by the service, a session ticket is used to authenticate the client for the duration of the session.
These tickets carry important information about the user or service account, the computer on which the request was made, and more. The information in the tickets is encrypted and can be accessed only by the party that requested the ticket or granted the access.
What are service principal names (SPNs)?
SPNs are used to uniquely identify a service that has registered itself in Active Directory. Each SPN is associated with a specific service account in Active Directory and describes the service type. Some service type examples:
- Web services: A web server like IIS might use an SPN such as HTTP/webserver.domain.com to authenticate with AD.
- SQL services: Microsoft SQL Server instances register an SPN such as MSSQLSvc/servername.domain.com:1433 to enable Kerberos authentication.
- File services: A file server can have an SPN such as HOST/fileserver.domain.com.
- Custom applications: Enterprises often develop in-house applications that use AD and Kerberos for authentication. These applications might also register their SPNs.
When a user or a service wants to access an AD-registered service, it queries the relevant SPN to request the necessary service ticket, which the target service then validates. Service accounts in Active Directory are vital as they may run critical applications or services and often have elevated privileges.
How does Kerberoasting work?
In a typical Kerberoasting attack:
- The attacker enumerates SPNs and their associated service accounts. Attackers can use PowerShell commands to easily find all SPNs of specific types. One of the most useful SPN types that attackers look for is SQL because it supports SQL Server (a popular target for data exfiltration).
- After identifying the available SPNs and their associated service accounts, the attacker requests the Kerberos ticket for the target SPNs and exfiltrates the ticket for decryption.
- The attacker then works offline to crack and decrypt the password hash for the ticket, using offline brute force tools and techniques.
- After cracking the ticket password, the attacker gains access to the (often privileged) account that is associated with the service ticket.
- The attacker uses the compromised account to perform privilege escalation and thus gain unauthorized access to sensitive information, to perform lateral movement, or to carry out other malicious activities.
- Compromising one account often enables the attacker to access additional user accounts on the server on which the attacker originally gained access. The attacker then uses the same technique to access more accounts.
What damage can Kerberoasting cause?
The risks posed by Kerberoasting are multifaceted. At its core, the attack leads to credential theft, putting sensitive service account credentials in the hands of adversaries.
What amplifies the threat is the permissions that service accounts might have. An attacker who cracks a high-privilege service account password can gain extensive access, opening doors to elevated privileges. Armed with these credentials, attackers can seamlessly move laterally within a network, accessing valuable data and resources.
Why is Kerberoasting such a popular attack?
Kerberoasting remains a common attack vector primarily because it can be challenging to identify and counteract. This attack is also relatively easy to execute using well-known tools.
Kerberos is engineered for both security and efficiency. However, its strength hinges on the confidentiality of the encryption keys that secure tickets during the authentication phase. If attackers manage to acquire these encryption keys (passwords), they can craft their own tickets, giving them a gateway to privileged information and network assets.
Achieving a successful Kerberoasting exploit on a Kerberos-dependent enterprise network might grant the attacker access to an expansive array of confidential data and tools. This explains why attackers are willing to put a lot of effort into Kerberoasting attempts.
Attackers can also orchestrate Kerberoasting remotely, sidestepping direct engagement with the authentication server or target assets. This stealthy approach makes Kerberoasting difficult for cybersecurity teams to spot and thwart in its early stages.
How can you defend against Kerberoasting?
Mitigating the risks posed by Kerberoasting involves several steps:
- Fortify service account passwords. Passwords should be unique, complex, and longer than 25 characters. They should be able to withstand brute force attacks, making it more difficult for attackers to crack the passwords associated with any service tickets they obtain. Change passwords at least once per year to help keep attackers at bay.
- If the relevant service supports it, use group managed service accounts (gMSAs) that provide password management to eliminate the need to manually manage service account passwords and to ease administrative overhead.
- Monitor Active Directory for anomalies such as abnormal or frequent service ticket requests. Such events might indicate a Kerberoasting attempt in progress.
- Adopt the principle of least privilege for service accounts. To ensure that applications work as expectd, these accounts are often over-privileged when set up. By limiting rights and permissions, you can minimize potential damage if an account is compromised.
- Consider disabling RC4 as an encryption type. Doing so can take time because you must ensure that down-level applications and systems can still work. However, this step is well worth the effort to ensure that passwords are no longer using this protocol to hash.
Another emerging defense against Kerberoasting is the deployment and monitoring of honey tokens. Essentially, these tokens are decoy accounts equipped with SPNs, left as bait for attackers. Because these accounts are fake and have no legitimate purpose, any activity surrounding them is a clear sign of malicious intent. With proper monitoring, they can alert your security team to a potential Kerberoasting attack, enabling you to defend against it and minimize any damage.
How Semperis can help you fight Kerberoasting
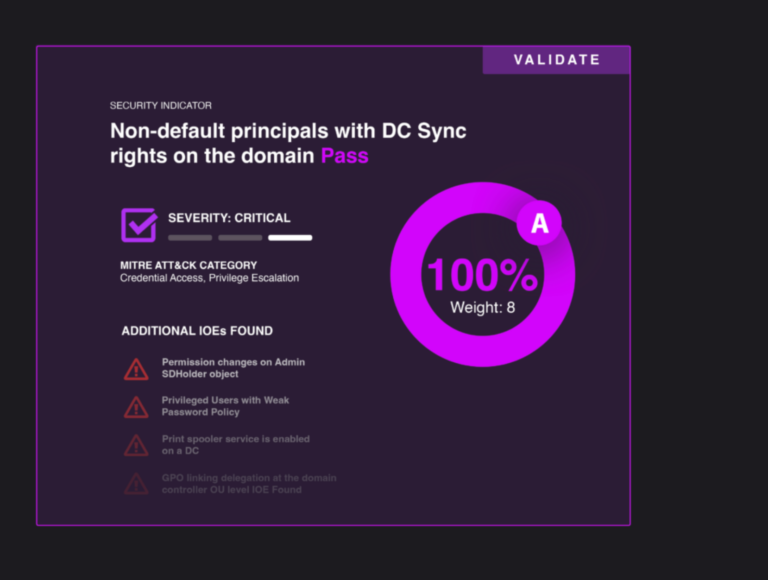
The evolving cyber-threat landscape demands tools that can keep pace. Advanced threat detection solutions like Semperis Directory Services Protector (DSP) can actively monitor, detect, and raise alerts for patterns consistent with Kerberoasting and other Active Directory–based attacks. Employing such tools amplifies your defense, making your AD environment more resilient against breaches.
Kerberoasting is a potent attack technique. However, you can effectively counter it with the right knowledge and tools. By understanding its mechanics, remaining vigilant, and deploying advanced security measures, enterprises can safeguard their Active Directory environments and the treasure trove of data to which they hold the keys.