- AD is still the cyber attacker’s fast lane
- Use the NIST CSF to focus incident response
- Identify: See your identity system clearly
- Protect: Shrink the blast radius
- Respond and Recover: Don’t let panic write your playbook
- Why this HIP session is worth your next hour
- Learn more about crisis management and incident response
Active Directory (AD) has passed its 25-year mark, and for most organizations, it’s still the backbone of identity. It’s also still the preferred highway for attackers aiming for domain dominance.
How can AD security improve crisis response?
In his Hybrid Identity Protection (HIP) Conference session A Quarter Century, a Quarter Million Breaches: AD Security & Incident Response, Microsoft Security MVP Michael Van Horenbeeck walks through why AD-centric attacks keep succeeding—and how a structured approach based on the NIST Cybersecurity Framework (CSF) can dramatically improve crisis management and incident response outcomes.
You can watch the full session recording here.
In 2026, “legacy” means critical, not obsolete. If you’re looking for ways to defend your identity infrastructure with confidence and build business resilience, start with these three high-value moves from Michael’s session.
Why is AD the cyber attacker’s fast lane?
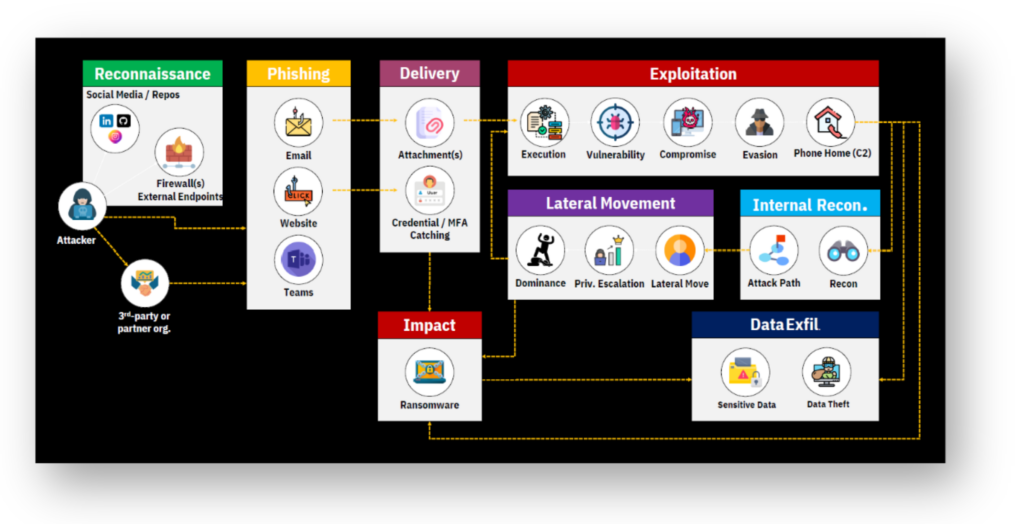
Despite the rise of Entra ID, most organizations still rely heavily on AD and will for years to come. That makes AD central to the steps in the modern cyber kill chain.
- Initial access on a single endpoint
- Internal reconnaissance to understand what’s connected where
- Lateral movement across systems using shared credentials and misconfigurations
- Privilege escalation to domain admins and Tier 0 systems
- Ransomware or data theft at scale
A hybrid identity infrastructure further raises the stakes. Firewalls, VPNs, Entra ID Connect, AD FS, and EDR tools can all become bridges between on-prem AD and the cloud—expanding potential attack paths in both directions.
You can’t flip a single setting to fix this. But you can organize how you defend, respond, and recover using the NIST CSF as your North Star.
Use the NIST CSF to focus your incident response effort where it counts
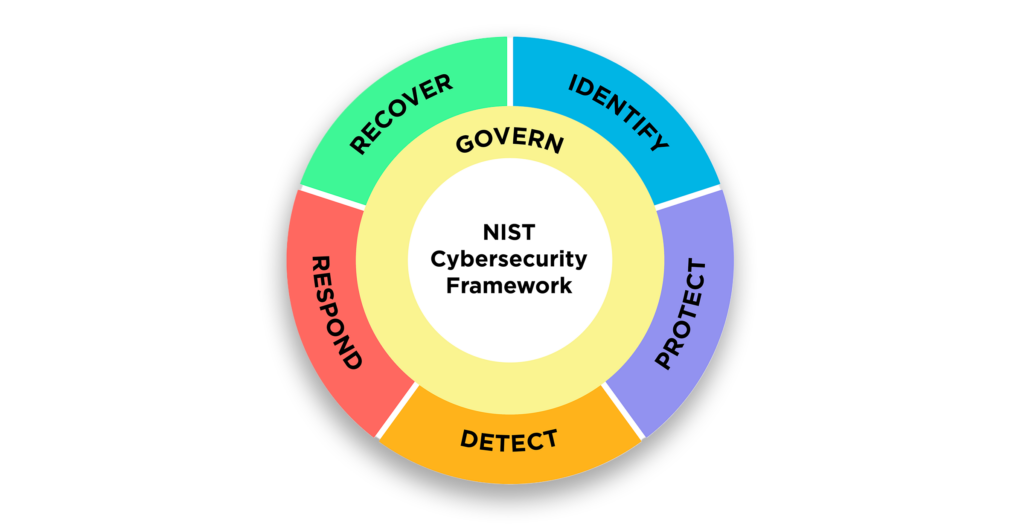
Michael maps AD and identity security work onto the six NIST CSF functions: Identify, Protect, Detect, Respond, Recover, Govern. For busy identity teams, three clusters of activity deliver especially high practical value for security posture and crisis management.
Identify: See your identity system clearly
Before you can manage an identity-driven crisis, you need visibility.
- Turn on meaningful logging on domain controllers and ship logs to a SIEM with enough retention to reconstruct events.
- Deploy Identity Threat Detection and Response (ITDR) capabilities to baseline “normal” activity and flag suspicious behavior in AD and Entra ID.
- Regularly run security assessment tools (such as Purple Knight) or continuous threat monitoring, detection, and response (such as with Directory Services Protector) to find misconfigurations, configuration drift, and indicators of exposure (IOEs) in AD and related services.
In a real incident response scenario, this evidence often makes the difference between controlled containment and flying blind.
Protect: Shrink the blast radius, not just the password list
Two of Michael’s strongest recommendations sit squarely in the Protect function. These activities pay off across incident response and recovery.
- Implement a tiered administration model. Define Tier 0 assets (e.g., domain controllers, AD CS, Entra ID Connect, virtualization hosts for DCs, key management systems) and isolate them with dedicated accounts, systems, and policies. A phished workstation admin should not be a straight line to domain dominance.
- Leverage Privileged Access Workstations (PAWs). Michael likens PAWs to the yellow hard hats on a construction site: mandatory safety gear. Admins use PAWs—locked down, internet-restricted machines—only for Tier 0 operations, following the “clean source” principle. That single design choice eliminates many routine lateral-movement paths into Tier 0 during a crisis.
These recommended Protect controls are as much crisis management activities as security hardening steps. They constrain how far an attacker (or a panicked admin) can move when things go wrong.
Respond and Recover: Don’t let panic write your playbook
In the Respond and Recover functions, Michael’s biggest warning is simple: Don’t panic-reset your way through a breach.
Resetting everything or turning off domain controllers can destroy evidence. Worse, it can create a false sense of safety, especially if attackers already have the keys to your identity kingdom (e.g., KRBTGT, NTDS.dit, forged tickets).
Instead, effective incident response and crisis management for AD look like this:
- Confirm you truly have an AD-related incident and define the scope.
- Identify attacker control paths: how they got in, how they move, what they can access.
- Safeguard at least one “known good” domain controller or site that hasn’t replicated malicious changes if possible—it can be a lifeline in recovery.
- Disable non-essential privileged accounts and use focused GPO changes to block high-risk logons, buying your team time to plan.
- Back up AD and Entra ID safely, then execute a tested recovery strategy based on business priorities, not guesswork.
This is where a NIST-aligned incident response plan intersects directly with organizational resilience. You’re not just putting out a fire—you’re preserving the ability to rebuild on purpose.
Why this HIP session is worth your next hour
This blog only scratches the surface of Michael’s guidance. View the full session to:
- Dive into real-world breach stories
- Walk through each incident response phase as it applies to AD
- Learn how to use the NIST CSF as a practical framework for ongoing hardening and crisis management
If AD or Entra ID appears anywhere in your job description, this talk is for you.
A Quarter Century, a Quarter Million Breaches: AD Security & Incident Response in 2025
Use this NIST-aligned lens to refine your own playbooks so that your next identity-centric incident is a managed crisis—not a career-defining catastrophe.
Learn more about crisis management and incident response
- Identity Recovery & Crisis Management: Inseparable for Incident Response
- Tech Talk | From Chaos to Control: Rethinking Cyber Crisis Management
- Tabletop to Reality: Building Cyber-Resilience Through Incident Response Drills
- Redefining Cyber Crisis Management | Semperis and Ready1
- The State of Enterprise Cyber Crisis Readiness | Semperis Reports
