Directory Services Protector

How We Recovered Active Directory From Cyberattack Hell
Tal Sarid, Semperis Director of Solutions, takes us through a real-life attack story in which a customer’s Active Directory was fully compromised. We used our Active Directory Forest Recovery (ADFR) solution to create a safety net, and ran our assessment tool, Purple Knight, to discover vulnerabilities. Our findings were significant:…
Understanding and Protecting Kerberos – The Soft Underbelly of Cybersecurity
With the advent of Active Directory more than 20 years ago, the Kerberos protocol was a game-changer in terms of security, unification, and moving AD into the realm of identity management. But times have changed. Newer and more sophisticated attack methods and the move to the cloud have left Kerberos…

The Top 10 Actions Every Organization Should Take to Protect their AD from Attacks
You know that cyber-attacks are coming. Maybe you’ve already been hit. Almost every attack is centered on finding a foothold in Active Directory, escalating privileges, and wreaking havoc. But did you know that there are some relatively simple actions you can take that will greatly increase your chances of fighting…
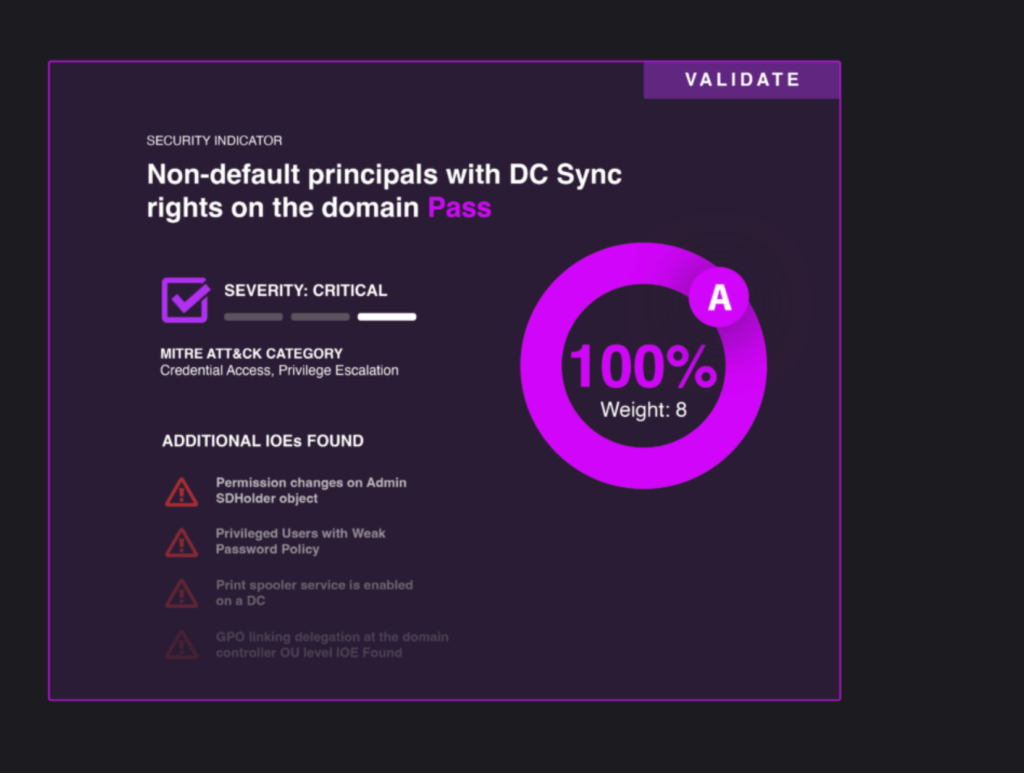
Would Your Organization Fail the Active Directory Security Assessment?
As cyberattacks proliferate, many organizations are investing resources in plugging holes in their security strategy. But one common attack entry point—also used in the SolarWinds breach—is consistently overlooked: Active Directory. According to results from a new security assessment tool that evaluates security weaknesses in Active Directory configurations, even large organizations…

Securing Active Directory—the Key Entry Point in Recent Cyberattacks
The health crisis of 2020 reshaped our view of how people work and how businesses run. As technology teams and processes have shifted to support remote workers and enable seamless supply-chain interactions, cybercriminals have seized opportunities to exploit the resulting gaps in security. As PWC recently reported, the number and…

A Swift Response to a Healthcare Ransomware Attack
Sirius Healthcare and Semperis help medical practice thwart devastating impacts, strengthen security stance When a private orthopedic specialty medical practice was threatened with a healthcare ransomware attack, it took swift action to minimize the impact. The medical practice's complex and distributed Microsoft Active Directory (AD) environment included more than 130…

Hybrid Active Directory Security Impact Report | 451 Research
It’s no surprise that directory services, particularly Microsoft’s Active Directory (AD), have become a prime target for attackers. Since AD is rarely safeguarded effectively, attackers have come to depend on weak configurations to identify attack paths, access privileged credentials, and get a foothold into target networks. Garrett Bekker, Senior Research Analyst…

Stepping up your Active Directory Defenses: Lessons Learned from Recent Attacks like PrintNightmare
Cybercriminals have been busy this summer, and many of the attacks have targeted Active Directory. In the month of July alone, attackers exploited Microsoft vulnerabilities that led to the PrintNightmare and PetitPotam attacks, in addition to other flaws that were not directly related to Active Directory. The REvil ransomware group…

Active Directory Hybrid Cloud Management: Top Security Risks to Watch For
Organizations are gravitating toward a hybrid identity management model: As cloud adoption increases, the ability to manage both on-premises and cloud access is a business requirement. For most companies, leveraging the cloud means integrating with Azure Active Directory (AAD). But integrating on-premises Active Directory with AAD authentication requires a different…

How Attackers Exploit Active Directory: Lessons Learned from High-Profile Breaches
Active Directory exploitation is the common thread in recent high-profile attacks. Colonial Pipeline, SolarWinds, Hafnium – every day we hear about a new attack, a new vulnerability, and devastating consequences. Almost every attack is centered on finding a foothold in Active Directory, escalating privileges, and wreaking havoc. The exposure is…



