Identity Threat Detection & Response
Categories
- Active Directory Backup & Recovery (67)
- Active Directory Security (231)
- AD Security 101 (17)
- Community Tools (25)
- Directory Modernization (9)
- From the Front Lines (69)
- Hybrid Identity Protection (76)
- Identity Attack Catalog (32)
- Identity Threat Detection & Response (161)
- Our Mission: Be a Force for Good (14)
- Purple Knight (5)
- Semperis University (5)
- The CISO's Perspective (16)
- Threat Research (77)
- Uncategorized (3)
EntraGoat Scenario 3: Exploiting Group Ownership in Entra ID
- Jonathan Elkabas and Tomer Nahum
- Nov 06, 2025
Dive into EntraGoat Scenario 3, where you’ll discover how individually legitimate Entra ID features, when combined with misconfigured group ownership, can cascade into a privilege escalation chain that elevates a low-level account into a tenant-wide threat.

Exploiting Ghost SPNs and Kerberos Reflection for SMB Server Privilege Elevation
- Andrea Pierini
- Oct 29, 2025
When misconfigured Service Principal Names (SPNs) and default permissions align, attackers can exploit Kerberos reflection to gain SYSTEM-level access remotely. Even with Microsoft’s security update, Ghost SPNs can still haunt you. Learn why.

Unlocking Unmatched Identity Resilience: The Semperis-Cohesity Partnership
- Chris Salzgeber | Product Manager, Integrations
- Sep 17, 2025
The Semperis-Cohesity partnership is the convergence of two industry leaders, each with singular expertise. With Cohesity Identity Resilience, organizations can be confident that their critical identity systems are secure and recoverable.

EntraGoat Scenario 6: Exploiting Certificate-Based Authentication to Impersonate Global Admin in Entra ID
- Jonathan Elkabas and Tomer Nahum
- Aug 12, 2025
Editor’s note This scenario is part of a series of examples demonstrating the use of EntraGoat, our Entra ID simulation environment. You can read an overview of EntraGoat and its value here. Certificate Bypass Authority–Root Access Granted EntraGoat Scenario 6 details a privilege escalation technique in Microsoft Entra ID where…
EntraGoat Scenario 2: Exploiting App-Only Graph Permissions in Entra ID
- Jonathan Elkabas and Tomer Nahum
- Aug 05, 2025
In our second EntraGoat attack scenario, follow the steps from a carelessly leaked certificate to capture the Global Admin password—and full Entra ID compromise.
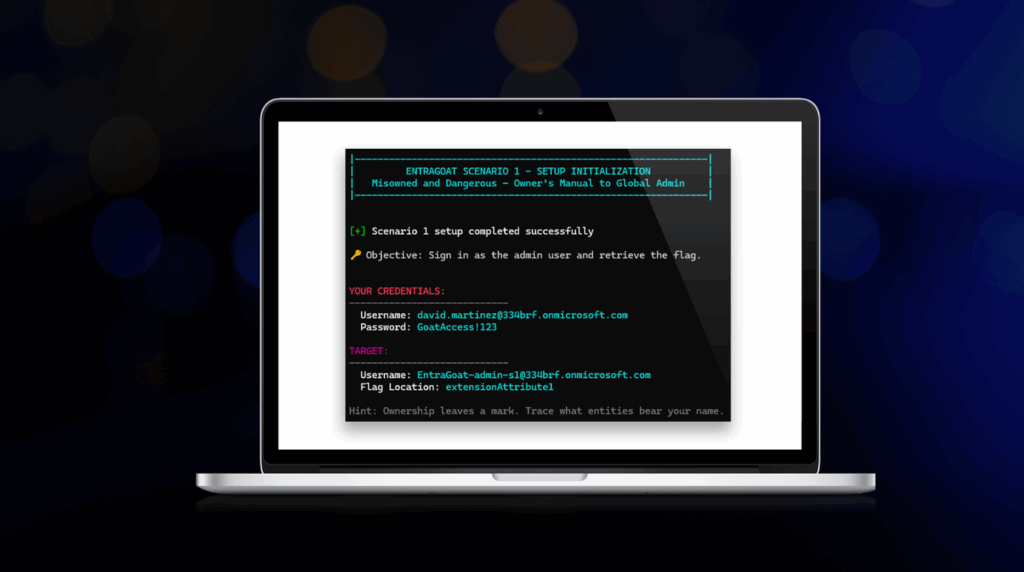
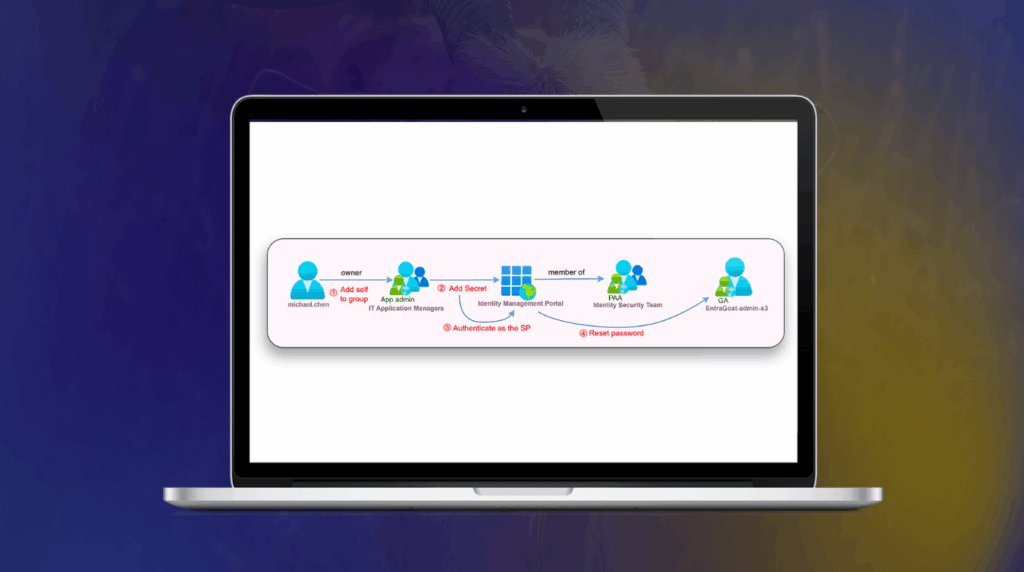
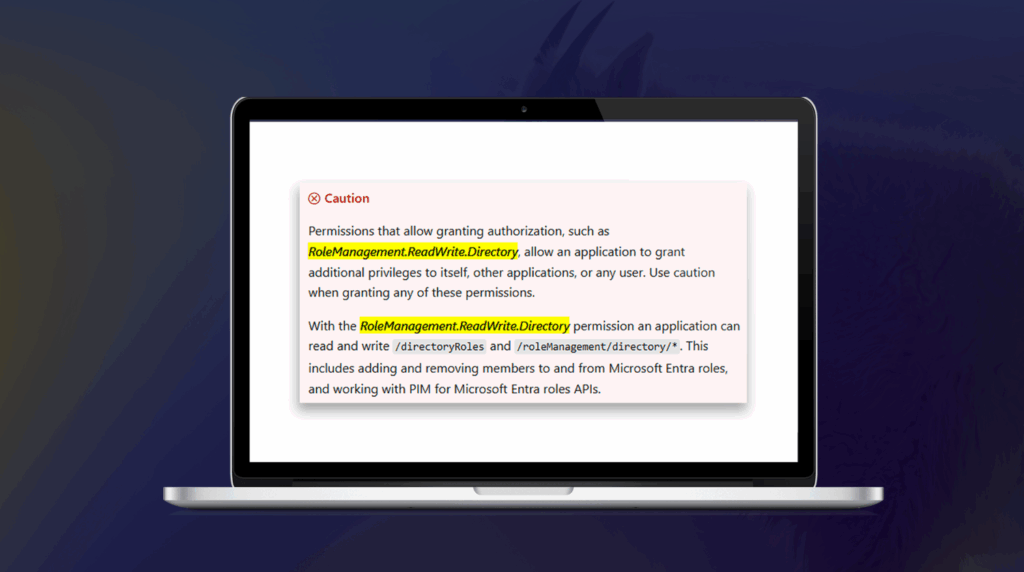
EntraGoat Scenario 1: Service Principal Ownership Abuse in Entra ID
- Jonathan Elkabas and Tomer Nahum
- Aug 05, 2025
How can a compromised low-privileged user account exploit service principal ownership—and complete an Entra ID tenant takeover? Find out when you dive into EntraGoat Scenario 1.

Getting Started with EntraGoat: Breaking Entra ID the Smart Way
- Jonathan Elkabas and Tomer Nahum
- Aug 04, 2025
Ready to jump in and get your hooves dirty in EntraGoat? Start here. These quick-start steps will get you into your first attack scenario.

What Is EntraGoat? A Deliberately Vulnerable Entra ID Simulation Environment
- Jonathan Elkabas and Tomer Nahum
- Aug 04, 2025
What’s the best way to build cyber resilience? Practice! Meet EntraGoat, your safe space for hands-on, CTF-style learning. Track attack paths, hunt down identity misconfigurations, and expose access control flaws—while building resilience against real-world threats.



