Webinar
Resilience in the Crosshairs: Best Practices for Securing Identity Systems Against Modern Threats
- Semperis
- Aug 18, 2025
Today's threat actors aren't just evolving—they're organizing. From ransomware gangs mimicking corporate structures to nation-state threats targeting critical infrastructure, security teams are facing an unrelenting wave of identity-based attacks. At the center of this onslaught is Active Directory (AD)—still the most common target for lateral movement and privilege escalation. In…

Using Lighting Intelligence for Continuous Saas Identity Security Assessment
- Semperis
- Jul 31, 2025
Lightning Intelligence is an easy-to-deploy SaaS security posture assessment tool for AD and Entra ID that automates identity environment scanning so you won’t miss emerging threats. In this video, Tammy Mindel, product owner of Purple Knight and Lightning Intelligence at Semperis, takes you for a tour of Lightning Intelligence: Learn…

Tech Talk — From Chaos to Control: Rethinking Cyber Crisis Management
- Semperis
- Jun 26, 2025
In today’s digital world, cyber incidents aren’t just IT issues—they’re full-blown business crises. Although many organizations have incident response plans in place, those plans often collapse under the pressure of a real-world event. In this webinar, Courtney Guss (Director of Crisis Management, Semperis) shares why traditional approaches to crisis management…
Cyber Resilience By Design
- Semperis
- Jun 13, 2025
Healthcare is a high-value target for threat actors and adversaries. Yet all too often, incident response plans rely on assumptions that can fall apart during a real crisis. In this focused webinar, you’ll learn why healthcare has a “cyber-crisis management crisis” and how organizations can achieve cyber and operational resilience.…

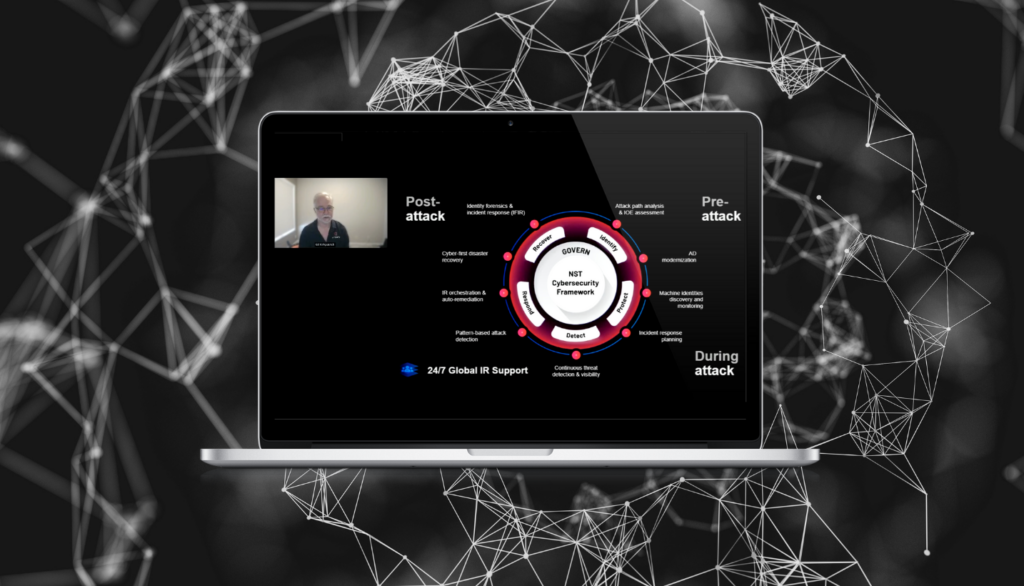
Beyond Defense: Active Directory Recovery and Business Resilience
- Semperis
Endpoint security, cyber insurance, and generalized disaster recovery plans are all important—but they won’t save your business from a major cyberattack. To keep operations running smoothly despite cyber threats, analysts and cybersecurity leaders recommend a focus on resilience. In this session, James Ravenell (Senior Solutions Architect, Semperis) explains why the…
Closing the Gap for Government Agencies: 5 Ways to Automate Cyber Resilience
- Semperis
Operational continuity depends on cyber resilience. Maintaining that resilience can be tricky when resources are scarce. Attackers know this and are skilled at turning staffing turnover and technology gaps to their advantage. Attackers’ favorite means of spreading malware, escalating privilege, and establishing perseverance is the identity infrastructure—typically Microsoft Active Directory…

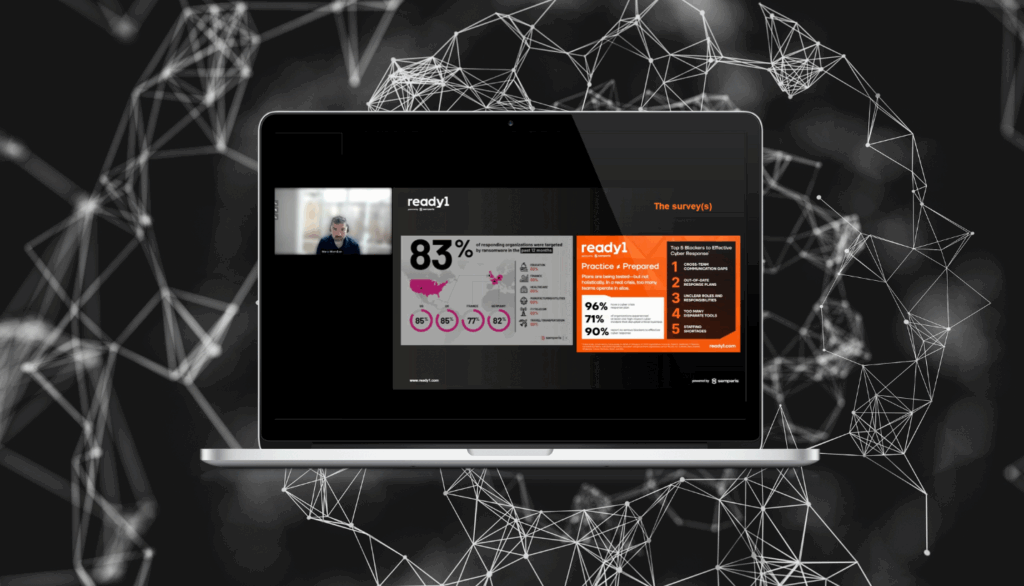
Achieving Resilience: Strengthening Business Through Cyber Incident Preparedness
- Semperis
In today’s threat landscape, attackers prioritize identity and access management systems like Microsoft’s Active Directory (AD) because they hold the keys to the kingdom in most enterprises. In other words, compromise AD, and you control the organization. That’s why modern cyber resilience strategies must focus on AD hardening, monitoring, and…

Tabletop to Reality: Building Cyber-Resilience Through Incident Response Drills
- Semperis
In today's threat landscape, the speed and effectiveness of your incident response can mean the difference between a minor setback and a catastrophic breach. The question isn't if a cyberattack will happen, but when—and preparation remains your strongest line of defense. Tabletop exercises aren't just practice—they're essential in exposing vulnerabilities,…

Why Is Your AD an Easy Target for Hackers?
- Semperis
Active Directory (AD) remains a cornerstone for many organizations, both on premises and integrated with Microsoft Entra ID in the cloud. Alarmingly, 90% of cyberattacks target AD, the central identity system for most enterprises. Semperis provides comprehensive protection for on-premises AD and Entra ID, offering continuous defense against identity-based threats before,…

Overcoming Vulnerabilities with Attack Surface Management
- Semperis
As the digital landscape expands, managing and securing the attack surface of your organization has never been more crucial. Join us for a hot topics webcast where industry experts will provide a comprehensive forecast of attack surface management (ASM) trends and offer strategic guidance for late 2024 and early 2025.…



