English

The State of Identity Security in the AI Era
Learn how organizations are managing the intersection of AI and identity resilience, based on our study of 1,100 IT and security professionals across eight countries.

Strengthen your Identity Resilience
Attackers don’t break in anymore, they simply log in. Microsoft Active Directory and Entra ID sit at the very heart of your enterprise. They control access, privilege, data and operational continuity. When compromised, they give cyber criminals near-total control of your environment which results in business disruption, data exposure, reputational…

Chris Inglis Joins the BBC Talking Business Program to Discuss Global Cyberattacks
Although organizations take cyber threats seriously, the reality is that most are not prepared for the full impact on their business when an attack happens. Former U.S. National Cyber Director and Semperis Strategic Advisor Chris Ingles joins the BBC’s Talking Business program to discuss how to meet the increasing global…

Bite-sized AD Security: Practical Steps to Strengthen Active Directory and Entra ID in 45 Minutes
- Semperis
- Dec 14, 2025
Small, smart steps to secure AD and Entra ID – without the project plan. Active Directory is still one of the top targets for ransomware and cyberattacks. Yet many IT teams admit they “just don’t have the time” to deal with it. Years of small misconfigurations and technical debt can…

2025 Ransomware Holiday Risk Report
Cyber attackers don’t take holidays. Our new study finds increased ransomware risk on holidays, weekends, and following material corporate events. Share this report with IT, security, and business stakeholders who need to understand ransomware attack behavior and defense trends—and how to strengthen your cyber resilience.
Active Directory Backup and Recovery at Polipol
What happens if Active Directory isn’t available because of a technical glitch or a cyberattack? A complete IT outage—which could cripple the entire global organization. Polipol took proactive measures to ensure business continuity—starting with Semperis ADFR.

Top AI Attacks and How ITDR Can Prevent Them
- Semperis
- Nov 17, 2025
In this informative webinar, Semperis Chief Product Officer Alex Weinert explains how AI is enabling cyber attackers and how an effective ITDR strategy can help reduce attack impacts.
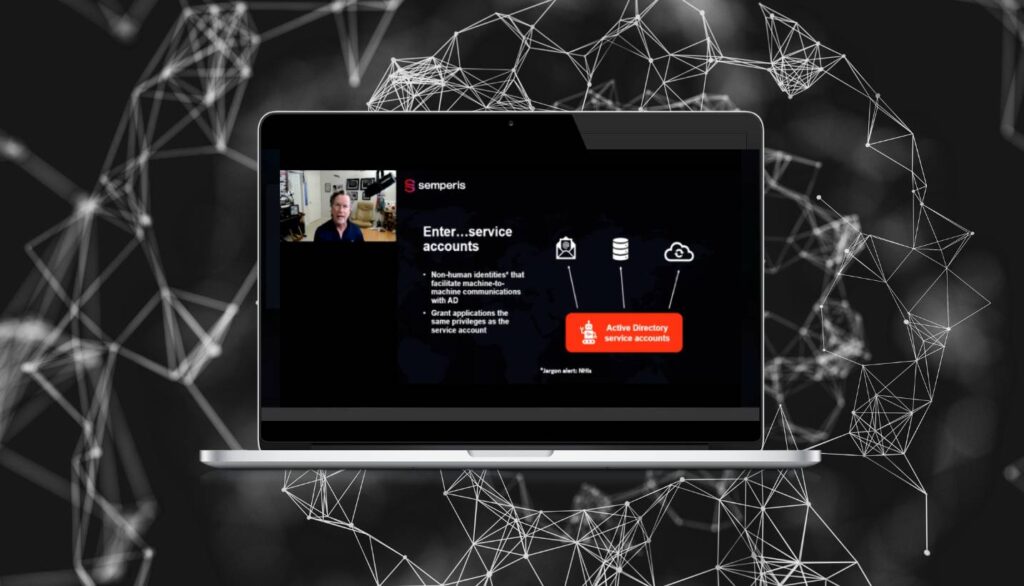
Mind the Gap: How to Secure Active Directory Service Accounts
- Semperis
- Nov 12, 2025
Service accounts are critical for enabling machine-to-machine communication in Active Directory (AD) environments. Email systems, databases, applications, even your security tools—all rely on service accounts for authentication. However, 94% of organizations lack full visibility into their service accounts. Learn how to close service account security gaps and strengthen IAM protection.
Defending the Public Sector: Confronting Cyber Threats with Limited Resources
- Semperis
- Oct 07, 2025
Public sector organizations are targets for today's most dangerous cyber adversaries, and resource and staffing shortfalls leave agencies vulnerable. Learn proven approaches to cyber crisis management and resilience that can help you close security gaps.
Resilience in the Crosshairs: Best Practices for Securing Identity Systems Against Modern Threats
- Semperis
- Aug 18, 2025
Today's threat actors aren't just evolving—they're organizing. From ransomware gangs mimicking corporate structures to nation-state threats targeting critical infrastructure, security teams are facing an unrelenting wave of identity-based attacks. At the center of this onslaught is Active Directory (AD)—still the most common target for lateral movement and privilege escalation. In…



